AI brokers with unrestricted net entry pose vital safety dangers. With out Chrome enterprise insurance policies to regulate browser conduct, an agent may navigate to unauthorized domains, retailer credentials within the browser’s password supervisor, or obtain information outdoors accredited workflows. Organizations with inner companies that use a personal certificates authority (CA) face a further barrier. Each HTTPS connection to these companies fails with certificates validation errors.
Amazon Bedrock AgentCore Browser now helps Chrome enterprise insurance policies and customized root CA certificates to present organizations granular management over agent browser conduct and connectivity. With Chrome insurance policies, you possibly can configure over 450 browser settings, together with URL filtering, obtain restrictions, and password supervisor controls, utilized by way of acquainted Chrome enterprise JSON configuration. Customized root CA assist lets your brokers hook up with inner companies and work with company SSL-intercepting proxies by trusting your group’s certificates authority. For the total reference of obtainable settings, see the Chrome Enterprise coverage listing.
On this put up, you’ll configure Chrome enterprise insurance policies to limit a browser agent to a selected web site, observe the coverage enforcement by way of session recording, and show customized root CA certificates utilizing a public check website. The walkthrough produces a working resolution that researches Amazon Bedrock AgentCore documentation whereas working below enterprise browser restrictions.
Why implement browser insurance policies for AI brokers
Chrome enterprise insurance policies handle three organizational wants when utilized to AI browser brokers.
First, you possibly can limit agent scope to accredited domains. URL allowlists and denylists restrict the place brokers can navigate. An agent tasked with processing invoices on a selected portal doesn’t want entry to social media or search engines like google. Insurance policies implement these boundaries on the browser degree, impartial of the agent’s immediate or reasoning.
Second, you possibly can disable dangerous browser options. With Chrome insurance policies, you possibly can flip off the password supervisor, block file downloads, disable autofill, and management dozens of different browser capabilities. For data-entry brokers that work together with delicate programs, these controls cut back the chance of unintended knowledge storage or exfiltration.
Third, you possibly can separate coverage administration from agent improvement. Managed insurance policies are configured on the browser degree by way of the management aircraft API and apply to each session created from that browser. This lets your safety crew outline accredited browser configurations whereas your improvement crew focuses on agent logic, with out embedding coverage choices in utility code.
How Chrome insurance policies and root CA certificates are utilized
The combination has two layers of coverage enforcement and an elective certificates belief configuration.
Managed insurance policies function on the browser degree. You present Chrome enterprise coverage JSON information saved in Amazon Easy Storage Service (Amazon S3) when making a browser by way of the management aircraft API. These insurance policies are saved by the service and enforced on each session created from that browser. Managed insurance policies map to Chrome’s /and so on/chromium/insurance policies/managed/ listing. They’ll’t be overridden by session-level settings.
Really helpful insurance policies function on the session degree. You may optionally present further coverage JSON information when beginning a browser session by way of the information aircraft API. These map to Chrome’s /and so on/chromium/insurance policies/advisable/ listing and performance as consumer preferences. If a managed coverage and a advisable coverage battle on the identical setting, the managed coverage takes priority. That is default Chrome conduct.
You should use customized root CA certificates to retailer your group’s root CA certificates in AWS Secrets and techniques Supervisor and reference it when making a browser or AgentCore Code Interpreter. The service imports the certificates into the certificates belief retailer, so connections to inner companies and SSL-intercepting proxies succeed with out disabling certificates validation.
Answer structure
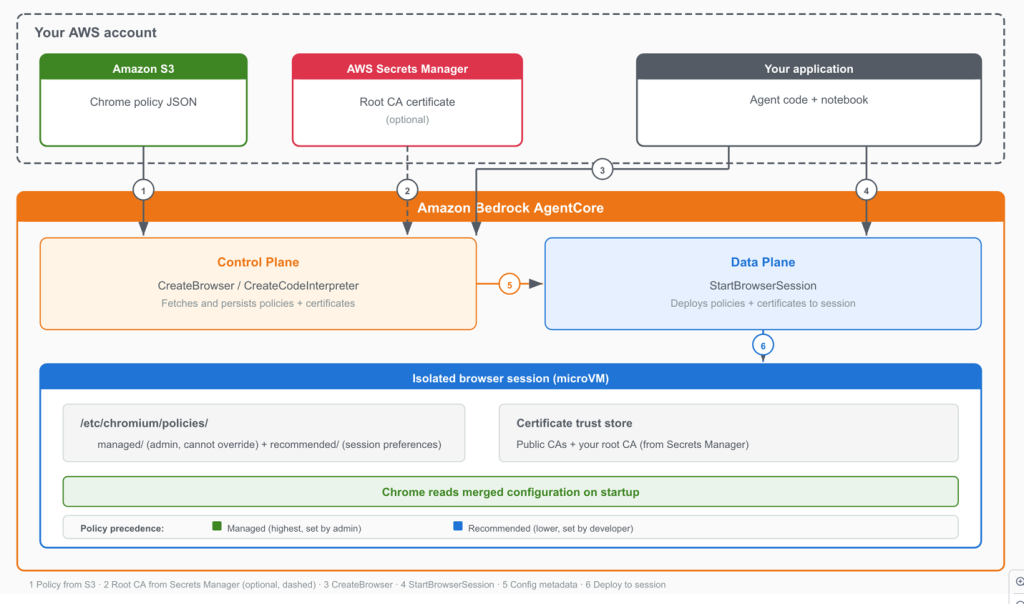
The next diagram exhibits how Chrome coverage JSON information and root CA certificates move out of your surroundings by way of the Amazon Bedrock AgentCore management aircraft and knowledge aircraft into the remoted browser session.
Determine 1: Coverage enforcement knowledge move out of your surroundings by way of Amazon Bedrock AgentCore to the remoted browser session.
- In your surroundings, you retailer Chrome coverage JSON information in Amazon S3 and elective root CA certificates in AWS Secrets and techniques Supervisor.
- The management aircraft fetches coverage JSON out of your S3 bucket once you name CreateBrowser (arrow 1) and fetches the foundation CA certificates from AWS Secrets and techniques Supervisor if configured (arrow 2, dashed to point this step is elective).
- Your utility calls the CreateBrowser API (arrow 3) after which the StartBrowserSession API (arrow 4).
- The management aircraft passes browser configuration metadata to the information aircraft (arrow 5).
- The information aircraft deploys managed insurance policies, advisable insurance policies, and root CA certificates to the remoted browser session (arrow 6). Chrome reads the merged configuration on startup and enforces the insurance policies all through the session.
Stipulations
Earlier than you start, confirm that you’ve the next:
- Python 3.10 or later
- An AWS account with Amazon Bedrock AgentCore entry enabled
- AWS credentials configured. You may confirm with
aws sts get-caller-identity - An AWS Area the place Amazon Bedrock AgentCore is out there (see Supported AWS Areas within the AgentCore documentation)
- Entry to an AI mannequin to drive the agent. This put up makes use of Anthropic Claude by way of Amazon Bedrock. AgentCore is model-agnostic. Different mannequin suppliers and agent frameworks could be substituted. For particulars on configuring totally different fashions with the Strands Brokers framework, see Mannequin Suppliers within the Strands Brokers documentation.
The pocket book creates the required AWS sources routinely, together with the S3 bucket, AWS Id and Entry Administration (IAM) execution function, AgentCore Browser, and AgentCore Code Interpreter. This computerized provisioning is meant for demonstration functions. Manufacturing deployments ought to use pre-existing sources with least-privilege IAM insurance policies reviewed by your safety crew. Seek advice from the pattern repository’s README for the whole IAM coverage particulars.
Necessary: Use short-term credentials from AWS IAM Id Middle or AWS Safety Token Service (AWS STS). Don’t use long-lived entry keys. Comply with the precept of least privilege when configuring IAM permissions.
Arrange the surroundings
The entire code for this walkthrough is out there as a Jupyter pocket book within the pattern repository. Clone it and run the cells in sequence.
Clone the repository
git clone https://github.com/awslabs/amazon-bedrock-agentcore-samples.git
cd amazon-bedrock-agentcore-samples/01-tutorials/05-AgentCore-tools/02-Agent-Core-browser-tool/13-browser-chrome-policiesArrange the surroundings
python3 -m venv .venv
supply .venv/bin/activate # On Home windows: .venvScriptsactivate
pip set up -r necessities.txtConfigure credentials
export AWS_REGION=us-west-2Necessary: Use short-term credentials. Don’t commit credentials to supply management.
Run the pocket book
jupyter pocket book browser-chrome-policies.ipynbRun the cells sequentially. Half 1 covers Chrome enterprise insurance policies. Half 2 covers customized root CA certificates. The next sections clarify what every half does and spotlight the important thing code.
Walkthrough
The pocket book is organized into two components. Half one creates a Chrome enterprise coverage, applies it to a customized AgentCore Browser, and makes use of Playwright to confirm that allowed URLs load whereas blocked URLs are rejected. Half two demonstrates customized root CA certificates with AgentCore Code Interpreter.
Outline the Chrome enterprise coverage
The primary pocket book cells outline a Chrome enterprise coverage that restricts the browser to AWS documentation and disables options that your agent doesn’t want. The coverage JSON makes use of commonplace Chrome enterprise coverage settings.
coverage = {
"URLBlocklist": ["*"],
"URLAllowlist": [
"docs.aws.amazon.com",
".aws.amazon.com",
".amazonaws.com",
],
"PasswordManagerEnabled": False,
"DownloadRestrictions": 3,
"DeveloperToolsAvailability": 0,
"BookmarkBarEnabled": False,
"AutofillAddressEnabled": False,
"AutofillCreditCardEnabled": False,
}The next desk describes every coverage setting.
| Coverage | Worth | Impact |
| URLBlocklist | [“*”] | Blocks URLs by default |
| URLAllowlist | docs.aws.amazon.com, .aws.amazon.com, .amazonaws.com | Permits AWS documentation and associated domains |
| PasswordManagerEnabled | false | Blocks credential storage |
| DownloadRestrictions | 3 | Blocks downloads |
| DeveloperToolsAvailability | 0 | Permits DevTools (required for CDP/Playwright automation) |
| BookmarkBarEnabled | false | Hides the bookmark bar |
| AutofillAddressEnabled | false | Disables handle autofill |
| AutofillCreditCardEnabled | false | Disables bank card autofill |
Notice that URLAllowlist makes use of Chrome’s URL filter sample format, which differs from typical glob patterns. Area patterns resembling docs.aws.amazon.com match the precise area. A number one dot, resembling .aws.amazon.com, matches subdomains. For the total sample syntax, see the URLAllowlist coverage documentation.
Additionally notice that DeveloperToolsAvailability should be set to 0 (or omitted) for browsers that can be used with Playwright or different CDP-based automation. AgentCore Browser automation makes use of the Chrome DevTools Protocol (CDP). Setting this coverage to 2 disables CDP on the Chrome degree, which silently breaks automation. The WebSocket connection succeeds on the proxy layer, however Chrome refuses CDP instructions, inflicting timeouts.
Create a browser with managed insurance policies
The following pocket book cells create a customized browser that enforces the coverage on each session. The important thing API name makes use of the enterprise_policies parameter with kind set to MANAGED. Session recording can also be enabled so you possibly can replay the session afterward.
from bedrock_agentcore.instruments import BrowserClient
shopper = BrowserClient(REGION)
response = shopper.create_browser(
title="docs_research_browser",
execution_role_arn=EXECUTION_ROLE_ARN,
network_configuration={"networkMode": "PUBLIC"},
enterprise_policies=[
{
"location": {
"s3": {
"bucket": BUCKET_NAME,
"prefix": POLICY_KEY,
}
},
"type": "MANAGED",
}
],
recording={
"enabled": True,
"s3Location": {
"bucket": BUCKET_NAME,
"prefix": "policy-demo",
},
},
)The pocket book then polls get_browser() till the standing transitions from CREATING to READY.
See the pattern pocket book for the whole code.
Show Chrome coverage enforcement with Playwright
The pocket book begins a browser session and makes use of Playwright to navigate to 2 URLs. The primary URL, docs.aws.amazon.com, is allowed by the coverage, so the web page hundreds efficiently. The second URL, www.wikipedia.org, is blocked by the coverage, so Chrome shows an error web page.
The check makes use of wait_until=”domcontentloaded” as a substitute of the default load occasion. AWS documentation pages have steady background community exercise from analytics scripts and monitoring pixels, which helps stop Playwright’s networkidle and default load states from resolving. Equally, textual content extraction makes use of web page.consider() to run JavaScript instantly within the browser context, which avoids Playwright’s selector engine timeouts on pages with steady DOM mutations.
After working this cell, it’s best to see output like the next:
TEST 1: Navigate to docs.aws.amazon.com (ALLOWED)
Web page title: Overview - Amazon Bedrock AgentCore
Web page textual content preview: Amazon Bedrock AgentCore ...
End result: PAGE LOADED SUCCESSFULLY
TEST 2: Navigate to www.wikipedia.org (BLOCKED)
Web page title:
End result: CHROME POLICY BLOCKED THIS URLThat is the core worth of Chrome insurance policies. The restriction occurs on the browser degree, impartial of the agent’s reasoning or immediate directions.
Whereas the cell runs, you possibly can watch the browser reside within the Amazon Bedrock AgentCore console. Navigate to Constructed-in instruments, choose your browser (docs_research_browser), and select View reside session for the lively session.
See the pattern pocket book for the whole code.
Evaluate the session recording
Since you enabled session recording when creating the browser, you possibly can replay the session to watch the coverage enforcement.
Open the Amazon Bedrock AgentCore console. Within the navigation pane, select Constructed-in instruments. Choose your browser device (docs_research_browser). Within the Browser classes part, discover the finished session with Terminated standing and select View Recording.
The session replay interface offers interactive video playback with a timeline scrubber, timestamped consumer actions together with every navigation occasion and the blocked try, and community occasions confirming that solely allowed site visitors succeeded.
Run a Strands Agent with the restricted browser (elective)
The pocket book consists of an elective cell that creates a Strands agent utilizing the policy-restricted browser. The agent researches AgentCore documentation throughout the allowed area. When it makes an attempt to navigate to an unauthorized URL, it observes that the web page is blocked and continues working with the accessible pages.
This pattern makes use of Anthropic Claude by way of Amazon Bedrock. AgentCore is model-agnostic. Different mannequin suppliers could be substituted. For mannequin configuration, see Mannequin Suppliers within the Strands Brokers documentation.
See the pattern pocket book for the whole code.
Show customized root CA certificates
Organizations that run inner companies with non-public CAs, or route site visitors by way of SSL-intercepting company proxies, want their brokers to belief these private certificates. AgentCore Browser and AgentCore Code Interpreter assist customized root CA certificates for this objective.
This part makes use of https://untrusted-root.badssl.com, a public web site that deliberately presents a certificates signed by an untrusted root CA. HTTPS connections to this website fail with certificates validation errors, identical to connections to your inner companies would fail with out the proper root CA.
The pocket book performs three steps.
Retailer the foundation CA certificates in AWS Secrets and techniques Supervisor
The BadSSL untrusted root CA certificates is publicly out there (supply: badssl.com/certs/ca-untrusted-root.crt). The pocket book saves it to AWS Secrets and techniques Supervisor in order that Amazon Bedrock AgentCore can import it into the certificates belief retailer. In a manufacturing surroundings, the group’s inner CA certificates or SSL-intercepting proxy root CA certificates could be positioned in Secrets and techniques Supervisor the identical manner.
Present the failure with out the foundation CA
The pocket book creates a default AgentCore Code Interpreter session and runs Python code that calls urllib.request.urlopen() towards the untrusted website. The connection fails with an SSLCertVerificationError. This is identical error you’ll see when connecting to inner company companies that use a personal CA.
Present success with the foundation CA
The pocket book then creates a customized AgentCore Code Interpreter that trusts the BadSSL root CA certificates utilizing the certificates parameter. This is identical sample already out there in BrowserClient.create_browser().
from bedrock_agentcore.instruments import CodeInterpreter, Certificates
ci_client_with_ca = CodeInterpreter(REGION)
response = ci_client_with_ca.create_code_interpreter(
title="demo_rootca_interpreter",
execution_role_arn=EXECUTION_ROLE_ARN,
network_configuration={"networkMode": "PUBLIC"},
certificates=[Certificate.from_secret_arn(secret_arn)],
)After working the identical urlopen() code towards the customized interpreter, the output exhibits Standing: 200. The connection succeeds as a result of the BadSSL root CA is now trusted. No code adjustments have been wanted. The belief was configured on the infrastructure degree.
See the pattern pocket book for the whole code.
Apply this to your group
The badssl.com demo mirrors two real-world situations.
| State of affairs | What you retailer in AWS Secrets and techniques Supervisor | Configuration |
| Inside company companies | Your group’s root CA certificates (the CA that indicators certificates in your HR portal, Jira, Artifactory, and related companies) | Reference the key ARN in certificates when making a browser or AgentCore Code Interpreter |
| SSL-intercepting company proxies | Your proxy’s root CA certificates (utilized by Zscaler, Palo Alto Networks, or related) | Reference the key ARN in certificates and configure proxy settings |
Customized root CA certificates work with each AgentCore Browser and AgentCore Code Interpreter. Within the browser, the certificates is imported into Chrome’s belief retailer. Within the interpreter, the service configures surroundings variables resembling REQUESTS_CA_BUNDLE and SSL_CERT_FILE in order that Python libraries belief the customized CA with out code-level workarounds.
You may mix root CA certificates with Chrome insurance policies in a single browser. The next instance creates a VPC-connected browser that trusts an inner CA and restricts navigation to a company intranet.
from bedrock_agentcore.instruments import BrowserClient, Certificates
response = shopper.create_browser(
title="internal_locked_down_browser",
execution_role_arn=EXECUTION_ROLE_ARN,
network_configuration={
"networkMode": "VPC",
"vpcConfig": {
"securityGroups": ["sg-0123456789abcdef0"],
"subnets": ["subnet-0123456789abcdef0"],
}
},
enterprise_policies=[
{
"location": {
"s3": {
"bucket": "org-policies",
"prefix": "intranet-only-policy.json",
}
},
"type": "MANAGED",
}
],
certificates=[
Certificate.from_secret_arn(
"arn:aws:secretsmanager:us-west-2:123456789012:secret:corp-root-ca"
)
],
)Clear up sources
To keep away from incurring fees, delete the sources that you just created. Run the cleanup cells on the finish of the pocket book, which cease lively browser classes, then delete the customized browser, AgentCore Code Interpreter, IAM function, Secrets and techniques Supervisor secret, and S3 coverage file.
Amazon Bedrock AgentCore Browser classes incur fees whereas lively. For pricing particulars, see Amazon Bedrock AgentCore pricing.
Conclusion
On this put up, you configured Chrome enterprise insurance policies to limit a browser agent to accredited domains and disabled dangerous browser options. You noticed the enforcement by way of reside view and session recording. You additionally demonstrated customized root CA certificates utilizing a public check website, displaying how AgentCore Code Interpreter classes can hook up with companies that use private CAs.
With these capabilities, you possibly can deploy AI brokers that function inside your group’s safety and compliance boundaries. Chrome insurance policies present browser-level controls managed independently from agent utility code. Customized root CA assist removes connectivity limitations to inner infrastructure.
Subsequent steps
Begin by making a browser with a URL allowlist tailor-made to your use case. The Chrome Enterprise coverage listing paperwork over 450 configurable settings. For data-entry brokers that work together with delicate types, contemplate disabling autofill and the password supervisor. For brokers that course of paperwork on a selected portal, limit downloads and restrict navigation to that portal’s area.
In case your group makes use of non-public PKI, configure root CA certificates and check connectivity to your inner companies. For brokers that function behind SSL-intercepting proxies, mix the foundation CA configuration with the proxy configuration function to route site visitors by way of your company proxy whereas trusting its certificates.
For extra details about Amazon Bedrock AgentCore Browser capabilities, see the Amazon Bedrock AgentCore Browser documentation. If in case you have suggestions, open a difficulty within the Amazon Bedrock AgentCore Python SDK repository.
Necessary: This pattern code is meant for improvement and demonstration. For manufacturing deployments, comply with the precept of least privilege for IAM permissions, limit Amazon S3 bucket insurance policies to licensed principals, rotate AWS Secrets and techniques Supervisor certificates earlier than expiration, and comply with the AWS Effectively-Architected Framework safety pillar.
Chrome is a trademark of Google LLC. All different logos are the property of their respective house owners.
Concerning the authors