As AI inference grows into a major share of cloud spend, understanding who and what are driving prices is important for chargebacks, value optimization, and monetary planning. At present, we’re saying granular value attribution for Amazon Bedrock inference.
Amazon Bedrock now routinely attributes inference prices to the IAM principal that made the decision. An IAM principal could be an IAM person, a task assumed by an software, or a federated id from a supplier like Okta or Entra ID. Attribution flows to your AWS Billing and works throughout fashions, with no assets to handle and no modifications to your current workflows. With elective value allocation tags, you possibly can mixture prices by workforce, undertaking, or customized dimension in AWS Price Explorer and AWS Price and Utilization Reviews (CUR 2.0).
On this put up, we share how Amazon Bedrock’s granular value attribution works and stroll via instance value monitoring eventualities.
How granular value attribution works
In your CUR 2.0, you possibly can see which AWS Id and Entry Administration (IAM) principals are calling Amazon Bedrock and what every is spending whenever you allow IAM principal knowledge in your knowledge export configuration, as proven within the following instance:
| line_item_iam_principal | line_item_usage_type | line_item_unblended_cost |
| arn:aws:iam::123456789012:person/alice | USE1-Claude4.6Sonnet-input-tokens | $0.069 |
| arn:aws:iam::123456789012:person/alice | USE1-Claude4.6Sonnet-output-tokens | $0.214 |
| arn:aws:iam::123456789012:person/bob | USE1-Claude4.6Opus-input-tokens | $0.198 |
| arn:aws:iam::123456789012:person/bob | USE1-Claude4.6Opus-output-tokens | $0.990 |
Right here, you possibly can see that Alice is utilizing Claude 4.6 Sonnet and Bob is utilizing Claude 4.6 Opus, and what every is spending in enter and output tokens. The next desk exhibits what the line_item_iam_principal column accommodates for every id kind:
| The way you name Amazon Bedrock Inference | line_item_iam_principal |
| AWS IAM Person | …person/alice |
| Bedrock key (maps to IAM Person) | …person/BedrockAPIKey-234s |
| AWS IAM Position (e.g. AWS Lambda operate) | …assumed-role/AppRole/session |
| Federated Person (e.g. from an id supplier) | …assumed-role/Position/person@acme.org |
Including tags for aggregation and Price Explorer
To mixture prices by workforce, undertaking, or value middle, add tags to your IAM principals. Tags circulate to your billing knowledge in two methods:
- Principal tags are hooked up on to IAM customers or roles. Set them as soon as they usually apply to each request from that principal.
- Session tags are handed dynamically when a person or software assumes an IAM function to acquire momentary credentials or embedded in id supplier assertions. To be taught extra, see Passing session tags in AWS STS.
After activation as value allocation tags in AWS Billing, each tag sorts seem within the tags column of CUR 2.0 with the iamPrincipal/ prefix, as proven within the following instance:
| The way you name Bedrock | line_item_iam_principal | tags |
| AWS IAM Person | …person/alice | {“iamPrincipal/workforce”:”ds”} |
| AWS IAM Position | …assumed-role/AppRole/session | {“iamPrincipal/undertaking”:”chatbot”} |
| Federated Person | …assumed-role/Position/person@acme.org | {“iamPrincipal/workforce”:”eng”} |
For extra steering on constructing a price allocation technique, see Finest Practices for Tagging AWS Sources.
Quickstart by state of affairs
Your setup depends upon how your customers and functions name Amazon Bedrock. The next desk summarizes the attribution obtainable in CUR 2.0 for every entry sample and what to configure for tag-based aggregation:
| Your setup | CUR 2.0 attribution | Find out how to add tags for aggregation + Price Explorer | Situation |
| Builders with IAM customers or API keys | Every person’s ARN seems in CUR 2.0 | Connect tags to IAM customers | 1 |
| Purposes with IAM roles | Every function’s ARN seems in CUR 2.0 | Connect tags to IAM roles | 2 |
| Customers authenticate via an IdP | session title in ARN identifies customers | Cross session title and tags out of your IdP | 3 |
| LLM gateway proxying to Bedrock | Solely exhibits gateway’s function (one id for all customers) | Add per-user AssumeRole with session title and tags | 4 |
Observe: For Eventualities 1–3, the line_item_iam_principal column in CUR 2.0 provides you per-caller id attribution. Tags are solely wanted if you wish to mixture by customized dimensions (workforce, value middle, tenant) or use Price Explorer for visible evaluation and alerts. For Situation 4, per-user session administration is required to get user-level attribution. With out it, site visitors is attributed to the gateway’s single function.
After including tags, activate your value allocation tags within the AWS Billing console or through UpdateCostAllocationTagsStatus API. Tags seem in Price Explorer and CUR 2.0 inside 24–48 hours.
The next sections stroll via a number of widespread eventualities.
Situation 1: Per-user monitoring with IAM customers and API keys
Use case: Small groups, improvement environments, or speedy prototyping the place particular person builders use IAM person credentials or Amazon Bedrock API keys.
The way it works:
Every workforce member has a devoted IAM person with long-term credentials. When both user-1 or user-2, for instance, calls Amazon Bedrock, Amazon Bedrock routinely captures their IAM person Amazon Useful resource Title (ARN) throughout authentication. Your CUR 2.0 exhibits who’s spending what.
If you wish to roll up prices by workforce, value middle, or one other dimension — for instance, to see whole spend throughout knowledge science workforce members — connect tags to your IAM customers. You possibly can add tags within the IAM console, AWS Command Line Interface (AWS CLI), or the AWS API. The next instance makes use of the AWS CLI:
# Tag the info science workforce's customers
aws iam tag-user
--user-name user-1
--tags Key=workforce,Worth="BedrockDataScience" Key=cost-center,Worth="12345"
aws iam tag-user
--user-name user-2
--tags Key=workforce,Worth="BedrockDataScience" Key=cost-center,Worth="12345"What seems in CUR 2.0:
The Price and Utilization Report captures each the person person id and their tags, supplying you with two dimensions for evaluation as proven within the following instance:
| line_item_iam_principal | line_item_usage_type | line_item_unblended_cost | tags |
| arn:aws:iam::123456789012:person/user-1 | USE1-Claude4.6Sonnet-input-tokens | $0.0693 | {“iamPrincipal/workforce”:”BedrockDataScience”,”iamPrincipal/cost-center”:”12345″} |
| arn:aws:iam::123456789012:person/user-1 | USE1-Claude4.6Sonnet-output-tokens | $0.2145 | {“iamPrincipal/workforce”:”BedrockDataScience”,”iamPrincipal/cost-center”:”12345″} |
| arn:aws:iam::123456789012:person/user-2 | USE1-Claude4.6Opus-input-tokens | $0.1980 | {“iamPrincipal/workforce”:”BedrockDataScience”,”iamPrincipal/cost-center”:”12345″} |
| arn:aws:iam::123456789012:person/user-2 | USE1-Claude4.6Opus-output-tokens | $0.9900 | {“iamPrincipal/workforce”:”BedrockDataScience”,”iamPrincipal/cost-center”:”12345″} |
The line_item_usage_type column encodes the area, mannequin, and token course (enter vs. output), so you possibly can reply questions like “How a lot did user-1 spend on Sonnet enter tokens vs. output tokens?” or “Who’s utilizing Opus vs. Sonnet?”
From this knowledge, you possibly can analyze prices in a number of methods:
- By person: Filter on
line_item_iam_principalto see precisely how a lot every particular person spent. That is helpful for figuring out heavy customers or monitoring particular person experimentation prices. - By mannequin: Filter on
line_item_usage_typeto match per-model spend, for instance, who’s driving Opus prices vs. Sonnet. - By workforce: Group by
iamPrincipal/workforceto see whole spend throughout knowledge science workforce members. That is helpful for departmental chargeback.
This strategy is good when you will have a manageable variety of customers and wish the only doable setup. Every person’s credentials immediately establish them in billing, and tags allow you to roll up prices to higher-level dimensions.
Utilizing Amazon Bedrock API keys: Amazon Bedrock additionally helps API keys for a simplified authentication expertise just like different AI suppliers. API keys are related to IAM principals. Requests made with API keys are attributed to the corresponding IAM identities, so the identical line_item_iam_principal and tag-based attribution applies. This implies organizations distributing API keys to builders or embedding them in functions can nonetheless observe prices again to the originating IAM person or function.
Situation 2: Per-application monitoring with IAM roles
Use case: Manufacturing workloads the place functions (not people) name Amazon Bedrock, and also you wish to observe prices by undertaking or service.
The way it works:
You may have two backend functions, for instance, a doc processing service (app-1) and a chat service (app-2). Every software runs on compute infrastructure (Amazon EC2, AWS Lambda, Amazon Elastic Container Service (Amazon ECS), and so on.) and assumes a devoted IAM function to name Amazon Bedrock. When both software calls Amazon Bedrock, the assumed-role ARN is routinely captured. This attribution flows to your CUR 2.0 report, supplying you with per-application value visibility.
You possibly can filter by line_item_iam_principal, which accommodates the function title, to see whole spend per software, or by line_item_usage_type to match mannequin utilization throughout companies. Tags are elective. In case your software generates distinctive session names per request or batch job, you possibly can observe prices at a good finer stage of element.
If you wish to roll up prices by undertaking, value middle, or one other dimension — for instance, to match whole spend throughout DocFlow vs. ChatBackend — connect tags to the IAM roles:
# Tag the doc processing function
aws iam tag-role
--role-name Position-1
--tags Key=undertaking,Worth="DocFlow" Key=cost-center,Worth="12345"
# Tag the chat service function
aws iam tag-role
--role-name Position-2
--tags Key=undertaking,Worth="ChatBackend" Key=cost-center,Worth="12345"When app-1 assumes Position-1 and calls Amazon Bedrock, the request is attributed to the assumed-role session. The function’s tags circulate via to billing routinely.
What seems in CUR 2.0:
The line_item_iam_principal exhibits the total assumed-role ARN together with the session title, as proven within the following instance:
| line_item_iam_principal | line_item_usage_type | line_item_unblended_cost | tags |
| arn:aws:sts::123456789012:assumed-role/Position-1/session-123 | USE1-Claude4.6Sonnet-input-tokens | $0.0330 | {“iamPrincipal/undertaking”:”DocFlow”,”iamPrincipal/cost-center”:”12345″} |
| arn:aws:sts::123456789012:assumed-role/Position-1/session-123 | USE1-Claude4.6Opus-output-tokens | $0.1650 | {“iamPrincipal/undertaking”:”DocFlow”,”iamPrincipal/cost-center”:”12345″} |
| arn:aws:sts::123456789012:assumed-role/Position-2/session-456 | USE1-NovaLite-input-tokens | $0.0810 | {{“iamPrincipal/undertaking”:”ChatBackend”,”iamPrincipal/cost-center”:”12345″} |
| arn:aws:sts::123456789012:assumed-role/Position-2/session-456 | USE1-NovaLite-output-tokens | $0.0500 | {“iamPrincipal/undertaking”:”ChatBackend”,”iamPrincipal/cost-center”:”12345″} |
This offers you a number of evaluation choices:
- Filter by function: See whole spend per software utilizing the function title portion of the ARN.
- Filter by session: Observe prices per request or batch job utilizing the session title.
- Mixture by undertaking: Group by
iamPrincipal/undertakingto match prices throughout DocFlow vs. ChatBackend. - Mixture by value middle: Group by
iamPrincipal/cost-centerto see whole spend throughout functions owned by the identical workforce.
This strategy is good for microservices architectures the place every service has its personal IAM function, a safety greatest observe that now doubles as a price attribution mechanism.
Situation 3: Per-user monitoring with federated authentication
Use case: Enterprise environments the place customers authenticate via a company id supplier (Auth0, Okta, Azure AD, Amazon Cognito) and entry AWS through OpenID Join (OIDC) or Safety Assertion Markup Language (SAML) federation.
The way it works:
Customers authenticate via your id supplier (IdP) and assume a shared IAM function. Per-user attribution comes from two mechanisms: the session title (person id embedded within the assumed-role ARN) and session tags (workforce, value middle, and so on. handed from the IdP). One IAM function serves the customers, so there are not any per-user IAM assets to handle.
The session title (highlighted in inexperienced) is what seems in line_item_iam_principal:
arn:aws:sts::123456789012:assumed-role/BedrockRole/user-1@acme.org
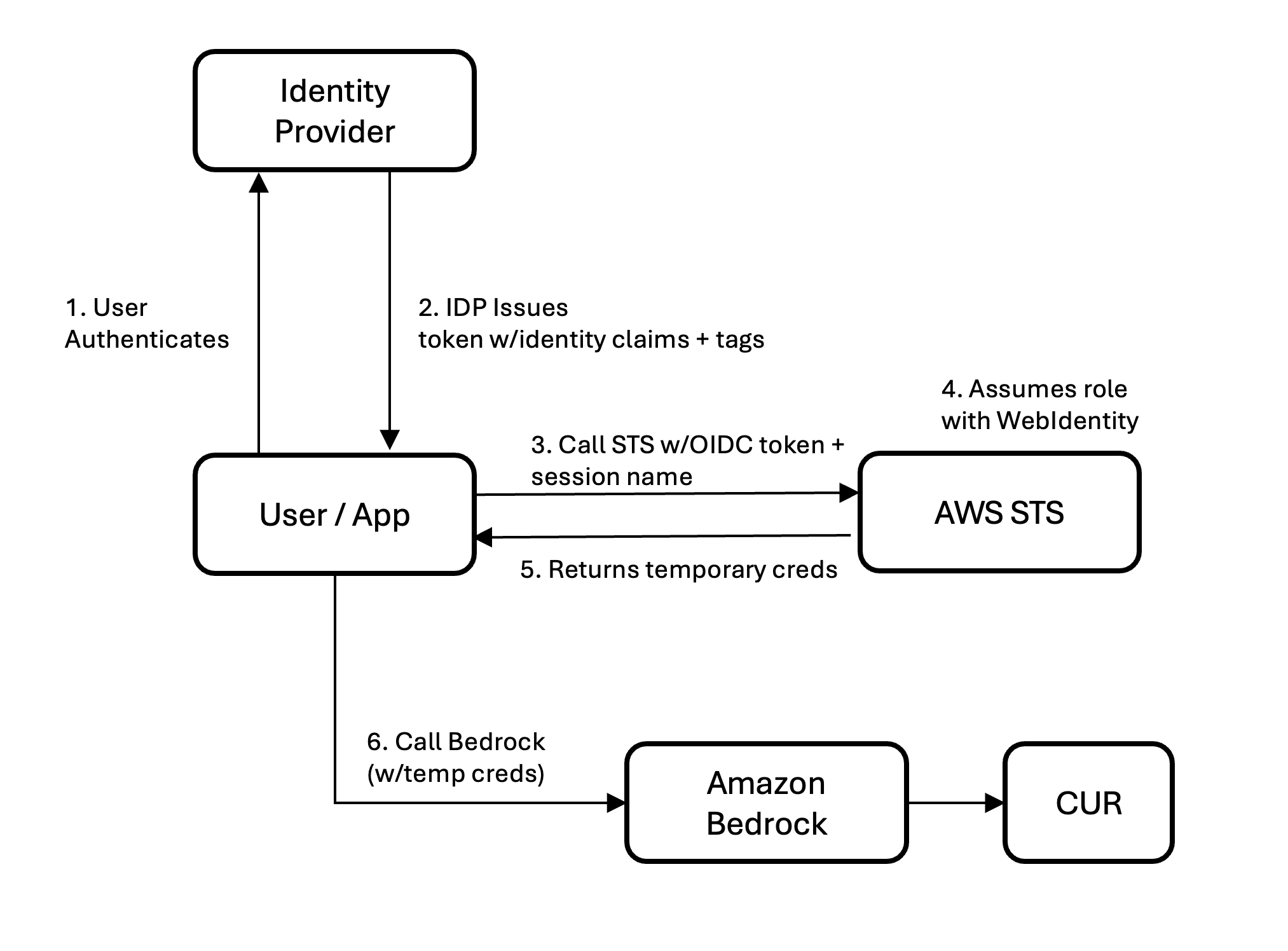
Determine 1. Id circulate in federated authentication eventualities
For OIDC federation (Auth0, Cognito, Okta OIDC): Register your IdP as an IAM OIDC supplier, create a task with a belief coverage permitting sts:AssumeRoleWithWebIdentity and sts:TagSession, and configure your IdP to inject the https://aws.amazon.com/tags declare into the ID token. AWS Safety Token Service (AWS STS) routinely extracts session tags from this declare. The calling software units –role-session-name to the person’s e mail (or one other identifier) when calling AssumeRoleWithWebIdentity.
For SAML federation (Okta, Azure AD, Ping, ADFS): Configure SAML attribute mappings in your IdP to cross RoleSessionName (e.g., person e mail) and PrincipalTag:* attributes (workforce, value middle) within the assertion. Each session title and tags are embedded within the signed assertion — the calling software doesn’t set them individually. The IAM function wants sts:AssumeRoleWithSAML and sts:TagSession.
In each circumstances, tags are cryptographically signed contained in the assertion or token so customers can not tamper with their very own value attribution.
What seems in CUR 2.0:
| line_item_iam_principal | line_item_usage_type | line_item_unblended_cost | tags |
| …assumed-role/Position-1/user-1@acme.org | USE1-Claude4.6Opus-input-tokens | $0.283 | {“iamPrincipal/workforce”:”data-science”,”iamPrincipal/cost-center”:”12345″} |
| …assumed-role/Position-1/user-1@acme.org | USE1-Claude4.6Opus-output-tokens | $0.990 | {“iamPrincipal/workforce”:”data-science”,”iamPrincipal/cost-center”:”12345″} |
| …assumed-role/Position-1/user-2@acme.org | USE1-Claude4.6Sonnet-input-tokens | $0.165 | {“iamPrincipal/workforce”:”engineering”,”iamPrincipal/cost-center”:”67890″} |
| …assumed-role/Position-1/user-2@acme.org | USE1-Claude4.6Sonnet-output-tokens | $0.264 | {“iamPrincipal/workforce”:”engineering”,”iamPrincipal/cost-center”:”67890″} |
On this instance, user-1 is utilizing Opus and user-2 is utilizing Sonnet. Each share the identical IAM function, however every is individually seen. Group by iamPrincipal/workforce for departmental chargeback or parse the session title for per-user evaluation.
Situation 4: Per-user monitoring via an LLM gateway
Use case: Organizations operating a big language mannequin (LLM) gateway or proxy (LiteLLM, customized API gateway, Kong, Envoy, or a homegrown service) that sits between customers and Amazon Bedrock.
The issue: Gateways authenticate customers at their very own layer, then name Amazon Bedrock utilizing a single IAM function hooked up to the gateway’s compute. With out extra work, each Amazon Bedrock name seems in CUR 2.0 as one id with no per-user or per-tenant visibility.
The answer: Per-user session administration
The gateway calls AssumeRole on an Amazon Bedrock-scoped function for every person, passing the person’s id as --role-session-name and their attributes (workforce, tenant, value middle) as --tags. The ensuing per-user credentials are cached (legitimate as much as 1 hour) and reused for subsequent requests from the identical person. This requires two IAM roles. The primary is a gateway execution function with sts:AssumeRole and sts:TagSession permissions. The second is an Amazon Bedrock invocation function, trusted by the gateway function and scoped to Amazon Bedrock APIs.
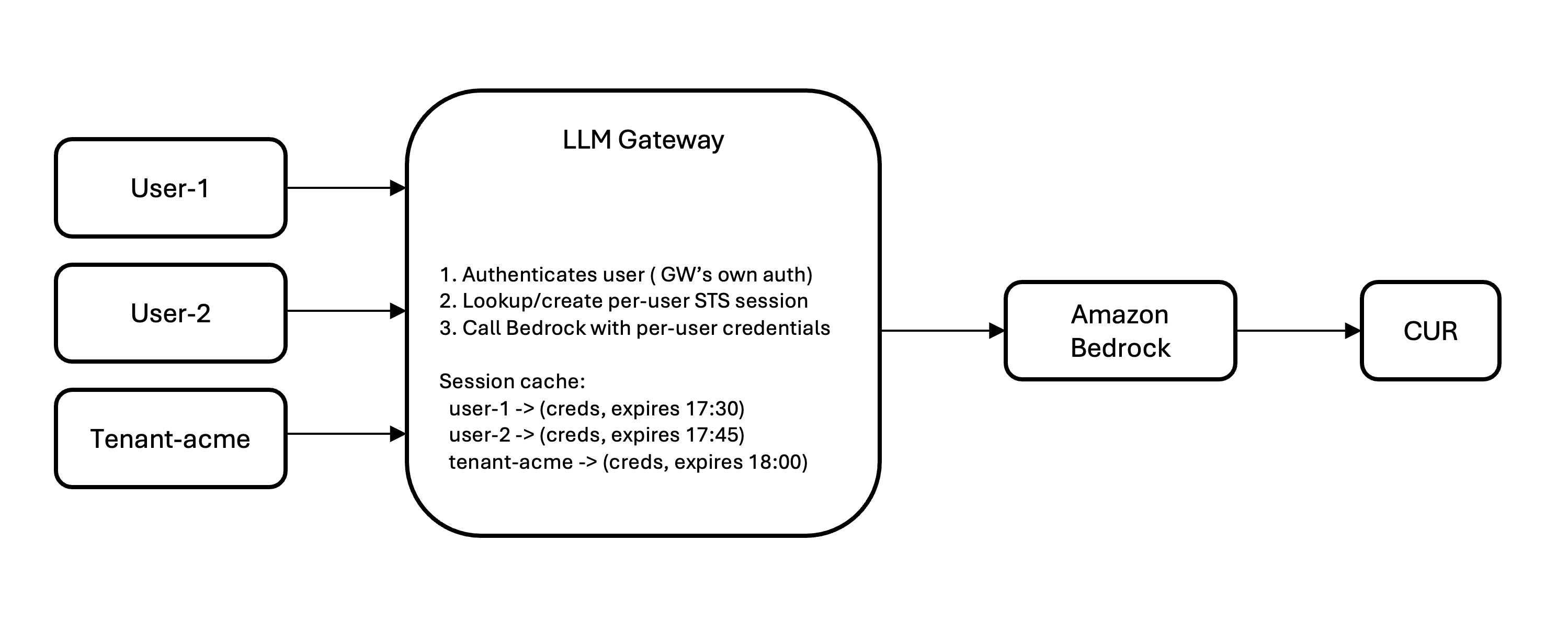
Determine 2. Id circulate in LLM Gateway eventualities
Key implementation issues:
- Cache classes:
AssumeRoleprovides minimal latency. With a 1-hour time to stay (TTL), you name STS as soon as per person per hour, not per request. - Cache measurement scales with concurrent customers, not whole customers (500 concurrent = ~500 cached classes).
- STS fee restrict is 500
AssumeRolecalls/sec/account by default. Request a rise for high-throughput gateways. - Session tags are immutable per session. Tag modifications take impact on subsequent session creation.
What seems in CUR 2.0:
| line_item_iam_principal | line_item_usage_type | line_item_unblended_cost | tags |
| …assumed-role/BedrockRole/gw-user-1 | USE1-Claude4.6Sonnet-input-tokens | $0.081 | {“iamPrincipal/workforce”:”data-science”} |
| …assumed-role/BedrockRole/gw-user-1 | USE1-Claude4.6Sonnet-output-tokens | $0.163 | {“iamPrincipal/workforce”:”data-science”} |
| …assumed-role/BedrockRole/gw-tenant-acme | USE1-Claude4.6Opus-input-tokens | $0.526 | {“iamPrincipal/tenant”:”acme-corp”} |
| …assumed-role/BedrockRole/gw-tenant-acme | USE1-Claude4.6Opus-output-tokens | $0.925 | {“iamPrincipal/tenant”:”acme-corp”} |
With out per-user session administration, gateway site visitors is attributed to the gateway’s single function. Including session administration is the important thing to unlocking per-user and per-tenant attribution.
Selecting your state of affairs
- Builders with IAM customers or Amazon Bedrock API keys → Situation 1
- Purposes/companies on AWS compute with IAM roles → Situation 2
- Customers authenticate via an IdP (Auth0, Okta, Azure AD) → Situation 3
- LLM gateway or proxy sitting in entrance of Amazon Bedrock → Situation 4
- Constructing a multi-tenant SaaS → Situation 4 with tenant ID as session title + session tags
- Claude Code workloads → Situation 3
Activating tags in AWS Billing
- Open the AWS Billing console
- Navigate to Price allocation tags
- After your tags have appeared in no less than one Amazon Bedrock request (permit as much as 24 hours), they seem within the AWS Administration Console below the IAM class
- Choose the tags you wish to activate and select Activate
For CUR 2.0, you’ll additionally must allow IAM principal when creating or updating your knowledge export configuration.
Viewing prices in Price Explorer
After you activate them, your IAM tags seem in Price Explorer’s Tags drop-down below the IAM class. You possibly can:
- Filter by workforce = data-science to see that workforce’s whole Amazon Bedrock spend
- Group by tenant to match prices throughout your clients
- Mix dimensions to reply questions like “How a lot did the engineering workforce spend on Claude Sonnet this month?”
Getting began
The brand new value attribution function for Amazon Bedrock is on the market now in industrial areas at no extra value. To get began:
- Determine your entry sample. Are builders calling Amazon Bedrock immediately with IAM customers or API keys (Situation 1)? Are functions utilizing IAM roles (Situation 2)? Do customers authenticate via an id supplier (Situation 3)? Or does site visitors circulate via an LLM gateway (Situation 4)?
- Allow IAM principal knowledge in your CUR 2.0. Replace your knowledge export configuration to incorporate IAM principal knowledge.
- Add tags if you happen to want aggregation or wish to filter in Price Explorer. Connect tags to IAM customers or roles, configure your IdP to cross session title and tags, or add per-user session administration to your gateway. Then activate your value allocation tags within the AWS Billing console.
- Analyze. Inside 24–48 hours of activation, your tags seem in Price Explorer and CUR 2.0. Filter by workforce, group by undertaking, or mix dimensions to reply questions like “How a lot did the engineering workforce spend on Claude Sonnet this month?”
Conclusion
Understanding who’s spending what on inference is step one to chargebacks, forecasting, and optimization. With granular value attribution for Amazon Bedrock, you possibly can hint inference requests again to a selected person, software, or tenant utilizing IAM id and tagging mechanisms you will have in place. Whether or not your groups name Amazon Bedrock immediately with IAM credentials, via federated authentication, or through an LLM gateway, AWS CUR 2.0 and AWS Price Explorer provide the visibility you want, at no extra value.
In regards to the authors