Organizations with customers in a number of geographies face information residency necessities reminiscent of Normal Information Safety Regulation (GDPR) in Europe, country-specific information sovereignty legal guidelines, and inner compliance insurance policies. Amazon Fast with Microsoft 365 extensions helps Regional routing to fulfill these necessities.
Amazon Fast helps multi-Area deployments so you’ll be able to route customers to AWS Area-specific Amazon Fast assets (Fast chat brokers, Fast Flows, information bases, and extra). Regulated industries reminiscent of monetary companies, healthcare, vitality, and telecommunications generally use this sample to maintain information inside particular geographical boundaries.
For those who combine Amazon Fast with Microsoft 365 functions, on this occasion Microsoft Groups, customers should authenticate and connect with their applicable Regional Amazon Fast assets. Regional routing makes positive customers entry the chat brokers and assets they construct of their Amazon Fast Area. On this submit, we are going to present you implement information residency when deploying Amazon Fast Microsoft Groups extensions throughout a number of AWS Areas. You’ll learn to configure multi-Area Amazon Fast extensions that robotically route customers to AWS Area-appropriate assets, serving to preserve compliance with GDPR and different information sovereignty necessities.
Answer overview
On this submit, we current a real-world instance with MyCompany, a fictional world group with European headquarters accessing Amazon Fast within the Europe (Eire) Area (eu-west-1) and a US department within the US East (N. Virginia) Area (us-east-1). A single Amazon Fast account has AWS Area-specific chat brokers (MyCompany-Data-Agent-eu-west-1 and MyCompany-Data-Agent-us-east-1) containing localized company info.
Regional routing requires AWS IAM Identification Middle with a trusted token issuer (TTI) for cross-system authentication. This submit makes use of Microsoft Entra ID for group-based entry management to exhibit how organizations can robotically route customers to their applicable AWS Areas, although different identification administration approaches are potential. This submit focuses on the Amazon Fast extension for Microsoft Groups as the first instance.
The next structure diagram demonstrates automate person routing throughout a number of AWS Areas by integrating Microsoft Entra ID with IAM Identification Middle. Through the use of Microsoft Entra ID group membership to direct customers to their designated Regional Amazon Fast deployments, you’ll be able to preserve information residency inside particular geographic boundaries whereas offering a constant expertise on your world workforce.
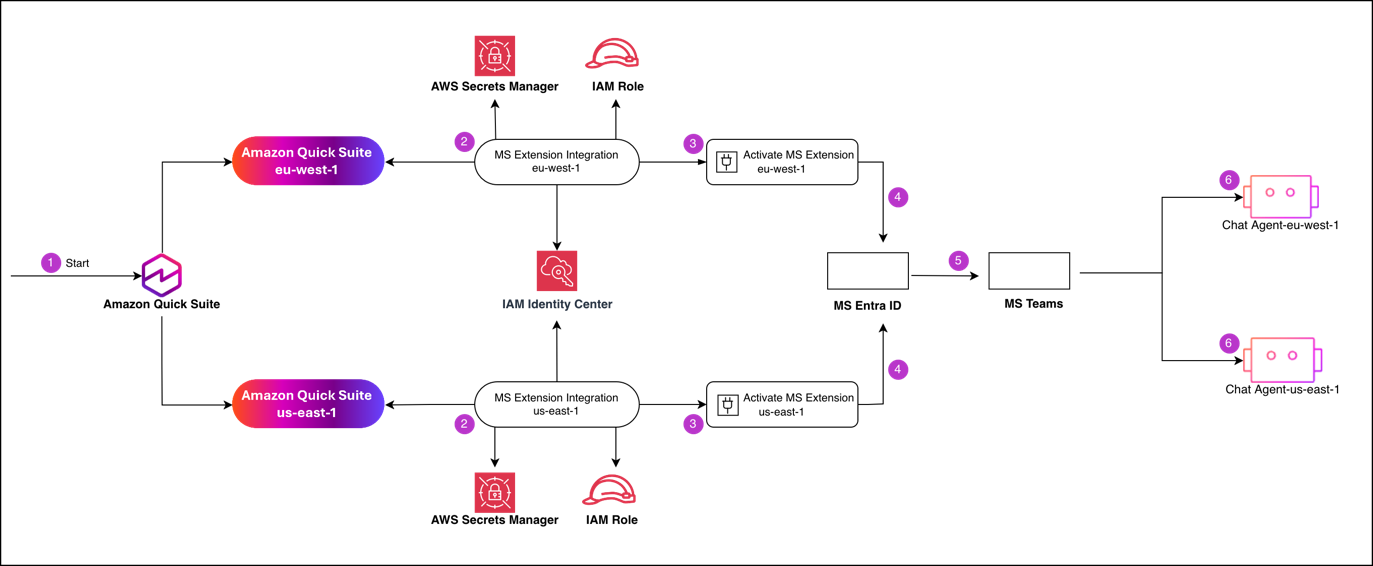
To implement this design, you’ll comply with a multi-phase course of that begins with AWS Administration Console configuration and concludes with the deployment of Regional add-ons to your customers. At a excessive degree, this submit exhibits you configure identification and belief one time, then repeat a small set of Regional steps per AWS Area. The next steps summarize the high-level workflow:
- Provoke setup on the Amazon Fast console and select the AWS Area to configure.
- Configure the Regional Microsoft Groups extension integration, together with an AWS Identification and Entry Administration (IAM) function and AWS Secrets and techniques Supervisor secret for that AWS Area, and belief IAM Identification Middle as a token issuer.
- Activate the extension in Amazon Fast to generate the Regional manifest file.
- Register the extension callbacks in your Microsoft Entra ID utility and full the activation callback for the applying throughout all AWS Areas.
- Deploy the Microsoft Groups add-on (
[YOUR_COMPANY_NAME]-Groups-[AWS_REGION]) to your Regional person teams by means of Microsoft Entra ID. - Map the Regional add-on to its designated information agent (
[YOUR_COMPANY_NAME]-Groups-[AWS_REGION] Agent) to grant customers entry to localized information.
Conditions
Your AWS setting should have Amazon Fast lively in your goal AWS Areas, together with the identification and secret administration companies used to deal with Regional authentication. For AWS companies, you could have the next in place:
- An lively Amazon Fast account
- IAM Identification Middle configured and managing person identities on your group with SAML integration with Microsoft Entra ID
- Secrets and techniques Supervisor accessible in each goal AWS Areas for storing authentication credentials
- IAM entry to create roles and insurance policies
For Microsoft 365, you could have the next for admin entry:
- A World Administrator or Utility Administrator function in Microsoft Entra ID
- Entry to Microsoft 365 Admin Middle for utility deployment
- Permissions to create and configure Enterprise functions in Microsoft Entra ID
Create Microsoft Entra ID utility
We begin by establishing the shared identification basis utilized by each AWS Area. On this first step, you create a Microsoft Entra ID utility. The Microsoft 365 extensions use the Microsoft Entra ID utility to authenticate customers towards Amazon Fast by means of IAM Identification Middle. Full the next steps to create your utility:
- In your Azure account, select App registrations, then select New registration.
- For Supported account sorts, select Accounts on this organizational listing solely (Private use solely – Single tenant).
- Select Register.
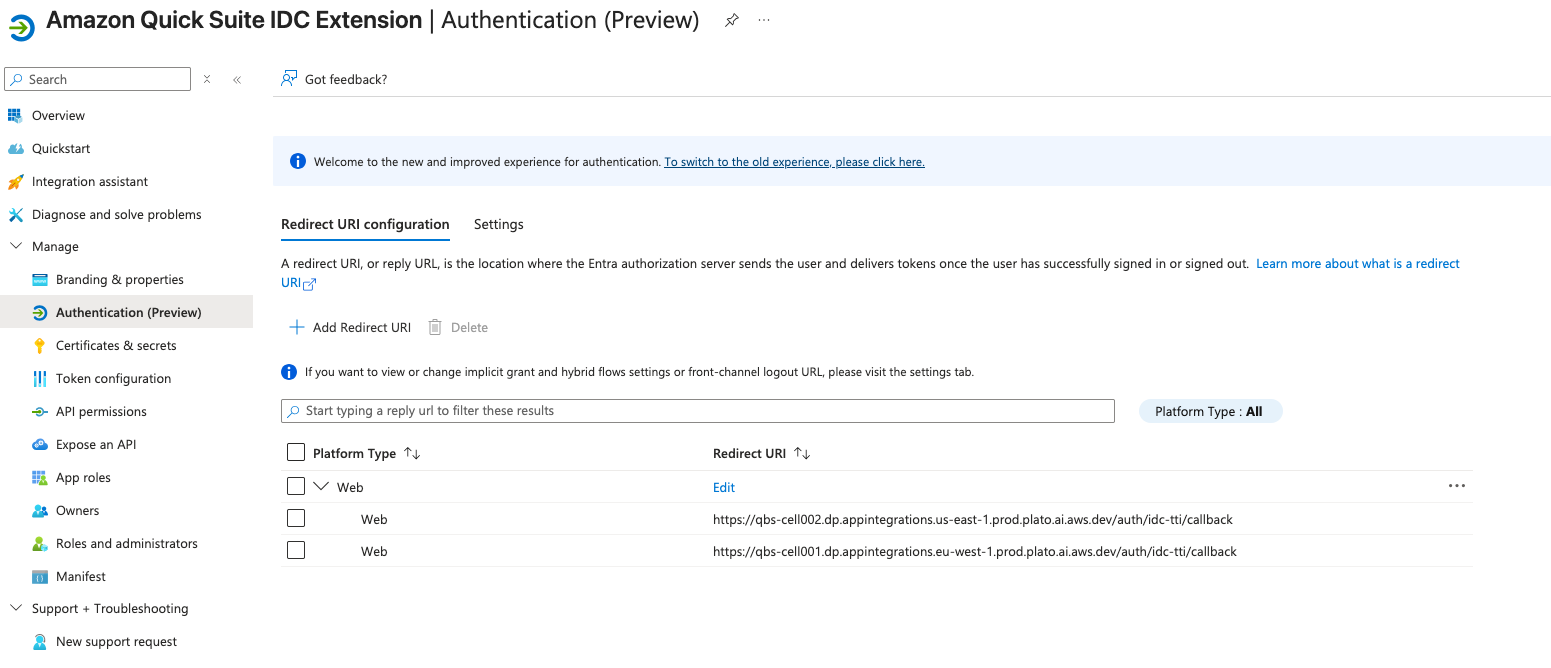
- Navigate to the applying registration’s Handle – Authentication tab.
- Select Add Redirect URL.
- Select Internet.
- For this submit, we use two redirect URLs, utilizing the sample
https://qbs-cell001.dp.appintegrations.[AWS_REGION].prod.plato.ai.aws.dev/auth/idc-tti/callback:https://qbs-cell001.dp.appintegrations.eu-west-1.prod.plato.ai.aws.dev/auth/idc-tti/callbackhttps://qbs-cell001.dp.appintegrations.us-east-1.prod.plato.ai.aws.dev/auth/idc-tti/callback
Microsoft Entra ID makes use of the callback URLs to return the person’s sign-in response to IAM Identification Middle for the proper AWS Area (eu-west-1 or us-east-1). Use these precise URLs—they’re the precise values required for Amazon Fast deployments.
- Grant the Microsoft Graph Person.Learn permission to permit the applying to check in customers and skim their fundamental profile info. This delegated permission doesn’t require admin consent.
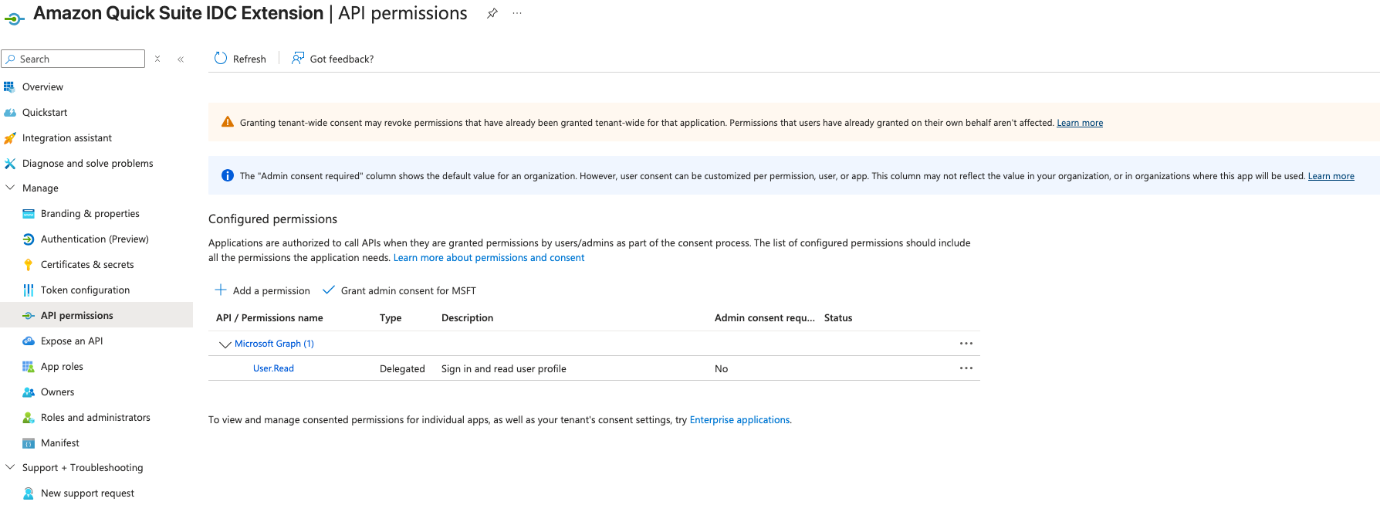
In subsequent steps, you will want your Microsoft tenant ID, utility consumer ID, and consumer secret worth.
Create trusted token issuer in IAM Identification Middle
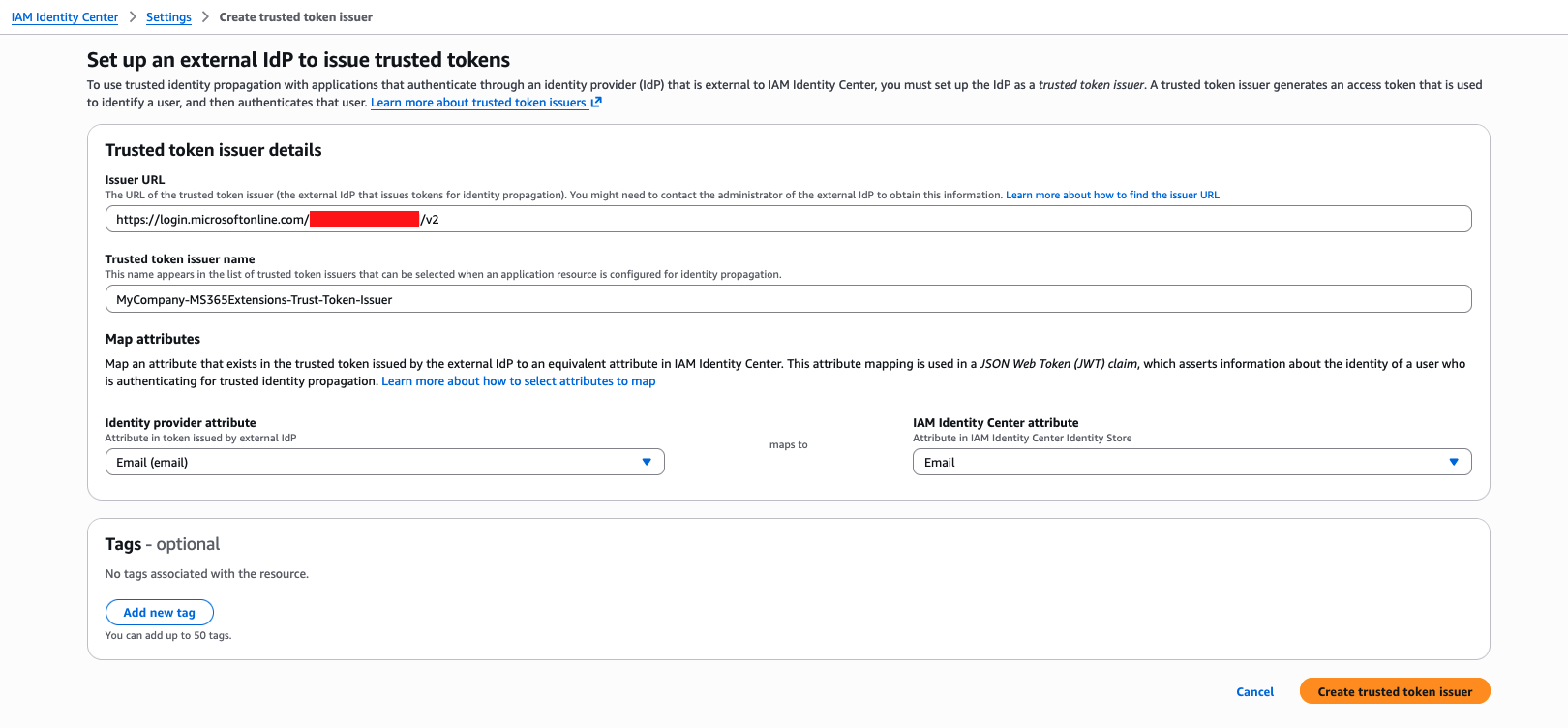
On this step, you create trusted token issuers in IAM Identification Middle. A trusted token issuer is a configuration in IAM Identification Middle that validates tokens issued by Microsoft Entra ID. You should utilize it for cross-system authentication, so customers can transfer between Microsoft 365 and AWS with out repeated sign-ins. Full the next steps to configure the trusted token issuer along with your Microsoft tenant’s issuer URL and map the e-mail attribute:
- On the IAM Identification Middle console, select Settings within the navigation pane.
- Select Create trusted token issuer.
- For Issuer URL, enter the URL on your trusted token issuer within the format
https://login.microsoftonline.com/[YOUR_TENANT_ID]/v2.0, utilizing the tenant ID you retrieved from the earlier step. - For Trusted token issuer identify, enter a reputation on your trusted token issuer within the format
[YOUR_COMPANY_NAME]-MS365Extensions-Belief-Token-Issuer, utilizing your organization identify. - Select Create trusted token issuer.
This configuration applies to every AWS Area the place you’ll be deploying the extensions.
With the worldwide identification parts in place, now you can configure every AWS Area with its personal secrets and techniques, roles, and extension settings that implement information residency for every geographic AWS Area.
Arrange IAM permissions and Secrets and techniques Supervisor entries
On this step, you create the mandatory secrets and techniques to retailer Microsoft 365 extension credentials and IAM permissions that grant learn entry to secrets and techniques.
Create one secret per AWS Area (eu-west-1 and us-east-1) in Secrets and techniques Supervisor following the identify conference [YOUR_COMPANY_NAME]/MS365/Extensions/[AWS_REGION]:
Create an IAM coverage referred to as [YOUR_COMPANY_NAME]-MS365-Extensions-Coverage:
Use the next belief relationship:
Every time you activate a brand new AWS Area, you could create a brand new secret in Secrets and techniques Supervisor and add the brand new secret Amazon Useful resource Title (ARN) to the Useful resource checklist within the IAM coverage. You will need to additionally add the brand new AWS Area you need to activate to the Service discipline within the IAM function belief relationship. This discipline identifies the Regional Service Principal, which is the precise AWS service identification (for instance, eu-west-1.prod.appintegrations.plato.aws.inner) that requires permission to imagine your IAM roles in that particular AWS Area.
Be aware of the created IAM function ARN. You will have it within the subsequent step.
Configure extensions in Amazon Fast
Full the next steps to create Amazon Fast managed extensions for Microsoft Groups:
- Sign up to the Amazon Fast console.
- Within the prime proper, select the profile icon.
- Select the EU (Eire) Area.
- On the drop-down menu, select Handle Fast.
- Beneath Permissions within the navigation pane, select Extension entry.
- Select Add extension entry.
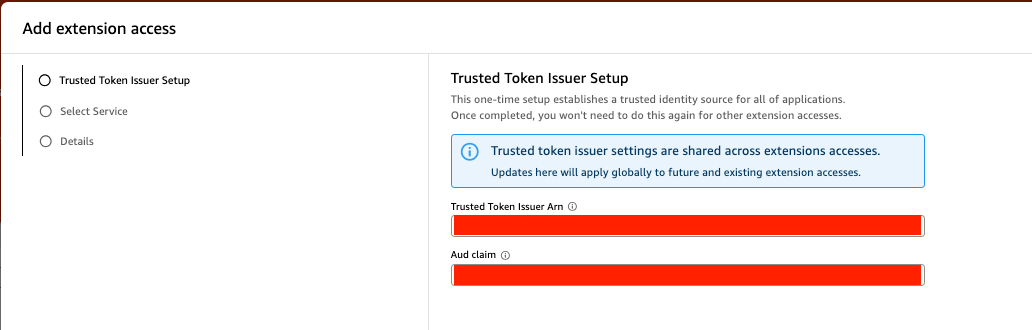
- Arrange your trusted token issuer:
- For Trusted Token Issuer Arn, enter the ARN for the trusted token issuer you created.
- For Aud declare, enter your consumer ID.
The Viewers (Aud) declare is a safety identifier that validates the authentication token is just utilized by the precise utility it was meant for, stopping unauthorized entry from different entities. These settings are shared throughout extension accesses on this AWS Area.
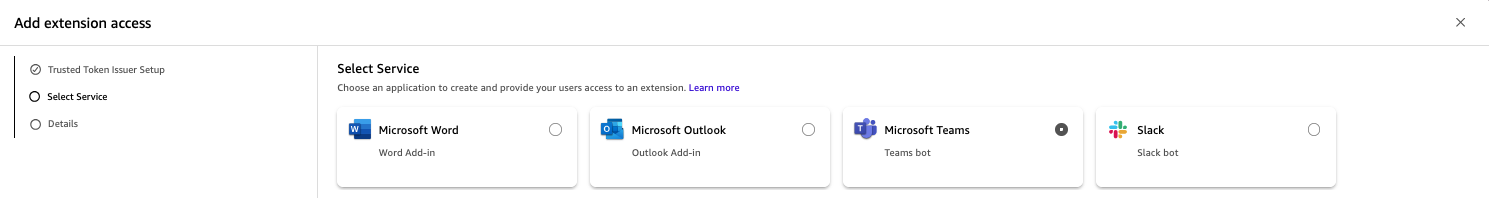
- Choose Microsoft Groups from the accessible extension sorts.
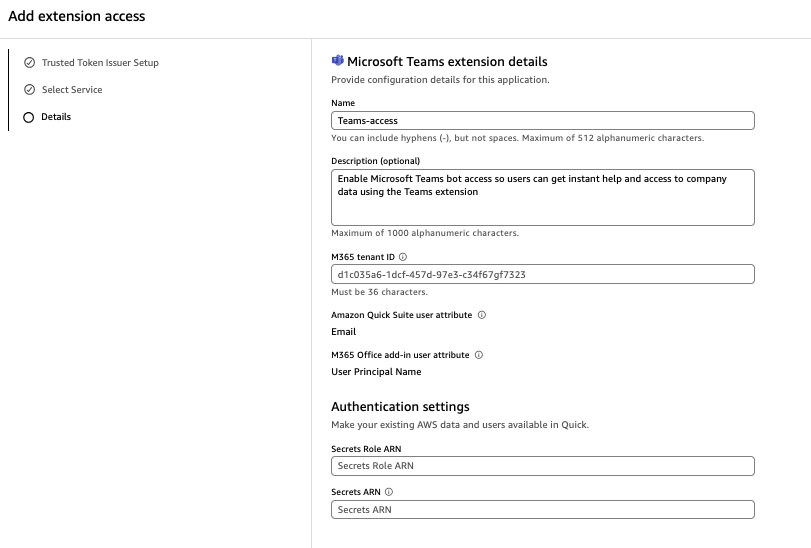
- Configure the extension along with your Microsoft 365 tenant ID, safety attributes, and authentication settings:
- Enter a reputation and non-obligatory description.
- For Microsoft tenant ID, enter your tenant ID.
- For Secrets and techniques Function ARN, enter the ARN on your Secrets and techniques Supervisor function.
- For Secrets and techniques ARN, enter the ARN on your secret. The ARN is Area-specific and should level to your Regional AWS assets.
- Return to the Amazon Fast console.
- Select Extensions within the navigation pane, then select Create extension.
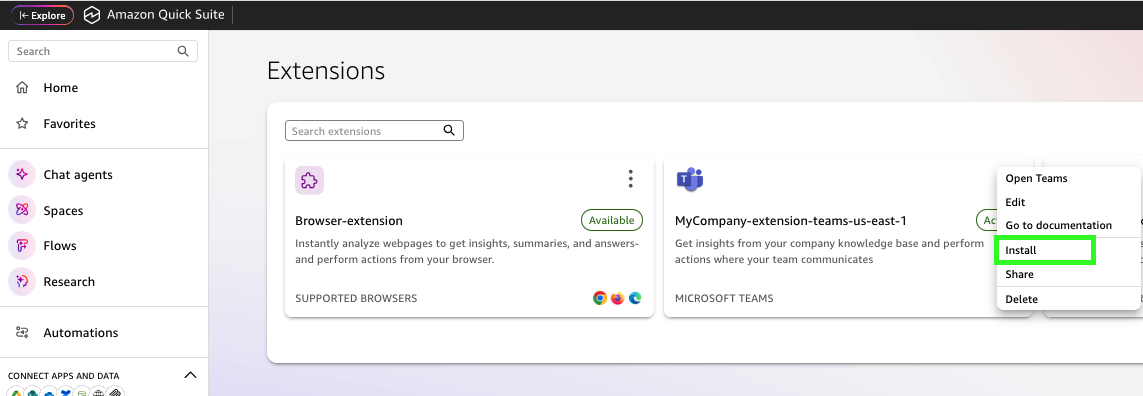
- Create a Microsoft Groups extension.
- Select the choices menu (three dots) subsequent to your extension and select Set up.
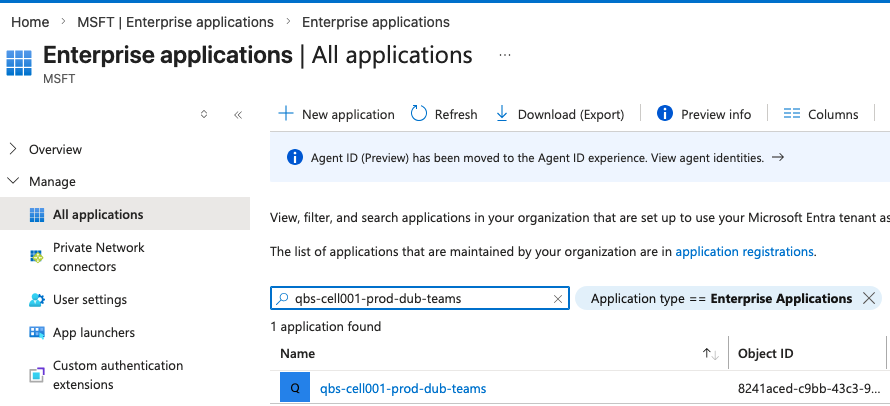
This course of creates an Enterprise utility in Microsoft Entra ID with the distinctive URLs and directions Microsoft 365 Groups wants to speak with the precise Regional AWS property. Utility set up requires permissions to put in an Enterprise utility in Microsoft Entra ID.
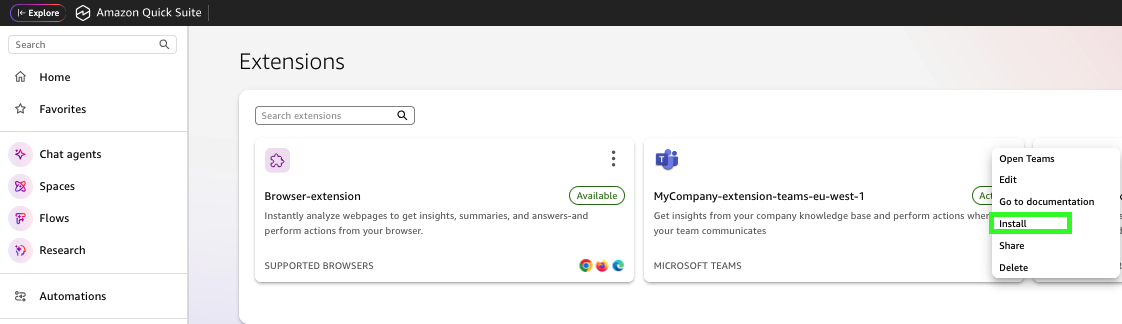
When the set up is full, the next entry shall be displayed within the Microsoft Entra ID Enterprise utility.
- Repeat these steps to create an extension and set up the applying within the
us-east-1Area. Comply with the identical naming conference with the AWS Area suffix, and use the key ARN for theus-east-1Area.
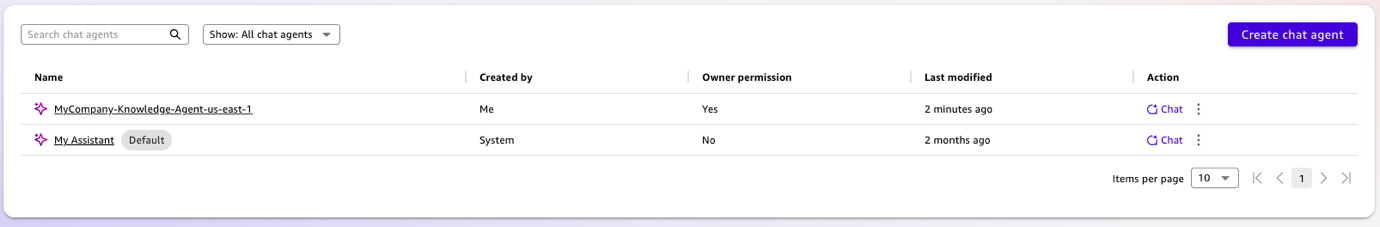
Create chat brokers
After the Regional functions are deployed, you create the AWS Area-specific chat brokers that every add-on will entry. Every AWS Area maintains its personal agent with localized information bases. Full the next steps:
- Open the Amazon Fast console in
eu-west-1. - Within the navigation pane, select Chat brokers, then select Create chat agent.
- Create a Regional chat agent in
eu-west-1with European company information. The naming conference consists of the AWS Area identifier for straightforward administration throughout a number of Areas:[YOUR_COMPANY_NAME]-Data-Agent-eu-west-1.
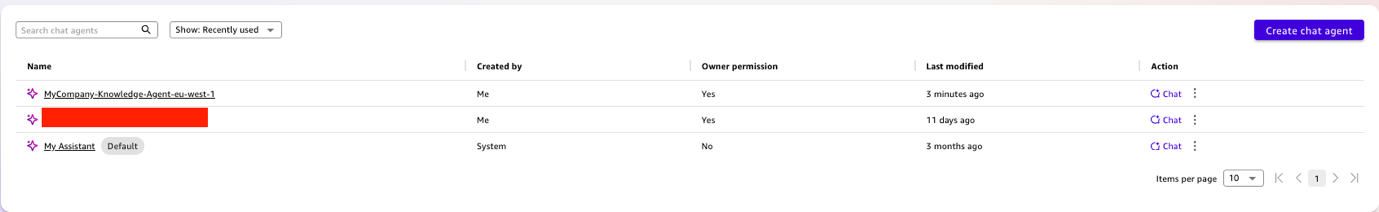
- Repeat these steps to create a chat agent in
us-east-1with US-specific company info, referred to as[YOUR_COMPANY_NAME]-Data-Agent-us-east-1.
The ultimate step is deploying the proper Regional add-on to the proper person group in Microsoft 365.
Deploy Microsoft Groups functions
Within the final step, you assign every Microsoft Groups utility to their respective Regional teams. Full the next steps:
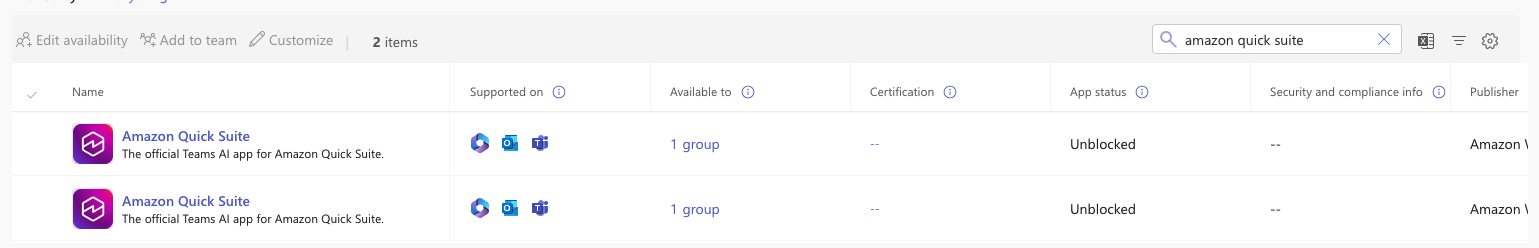
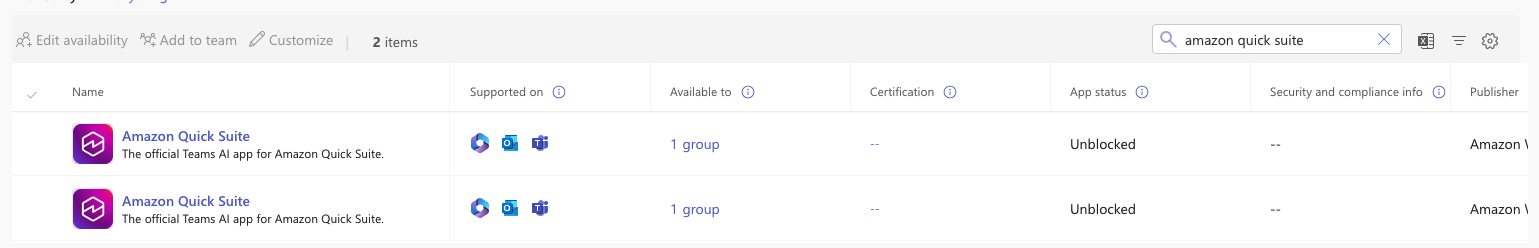
- In Microsoft Groups Admin Middle, select Workforce apps.
- Select Handle apps and filter the functions by “Amazon Fast.”
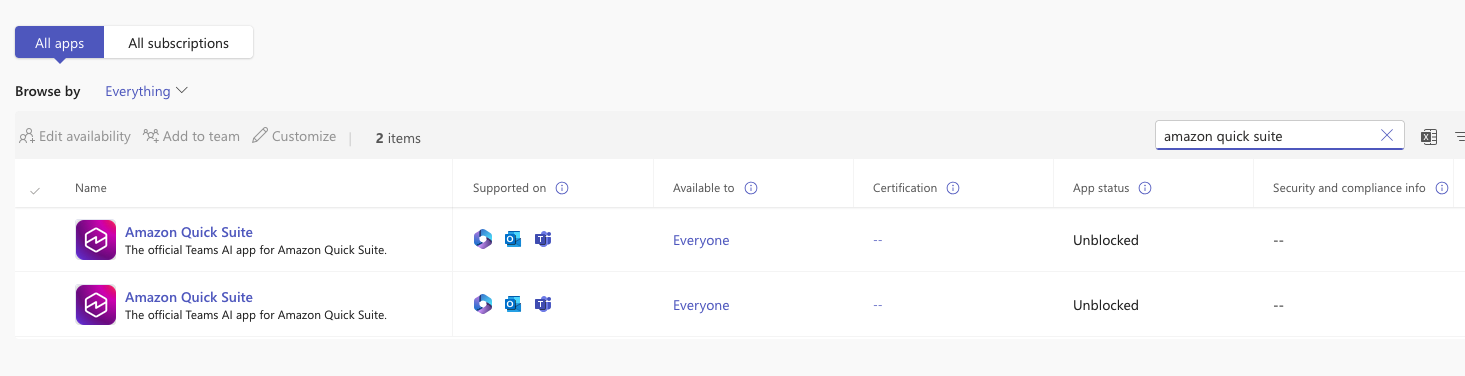
- Select on the primary utility (within the
eu-west-1Area) and select Edit Availability. - Assign the extension to particular Regional person teams relatively than your entire group. This group-based deployment robotically routes your customers to their right Regional Amazon Fast account assets.
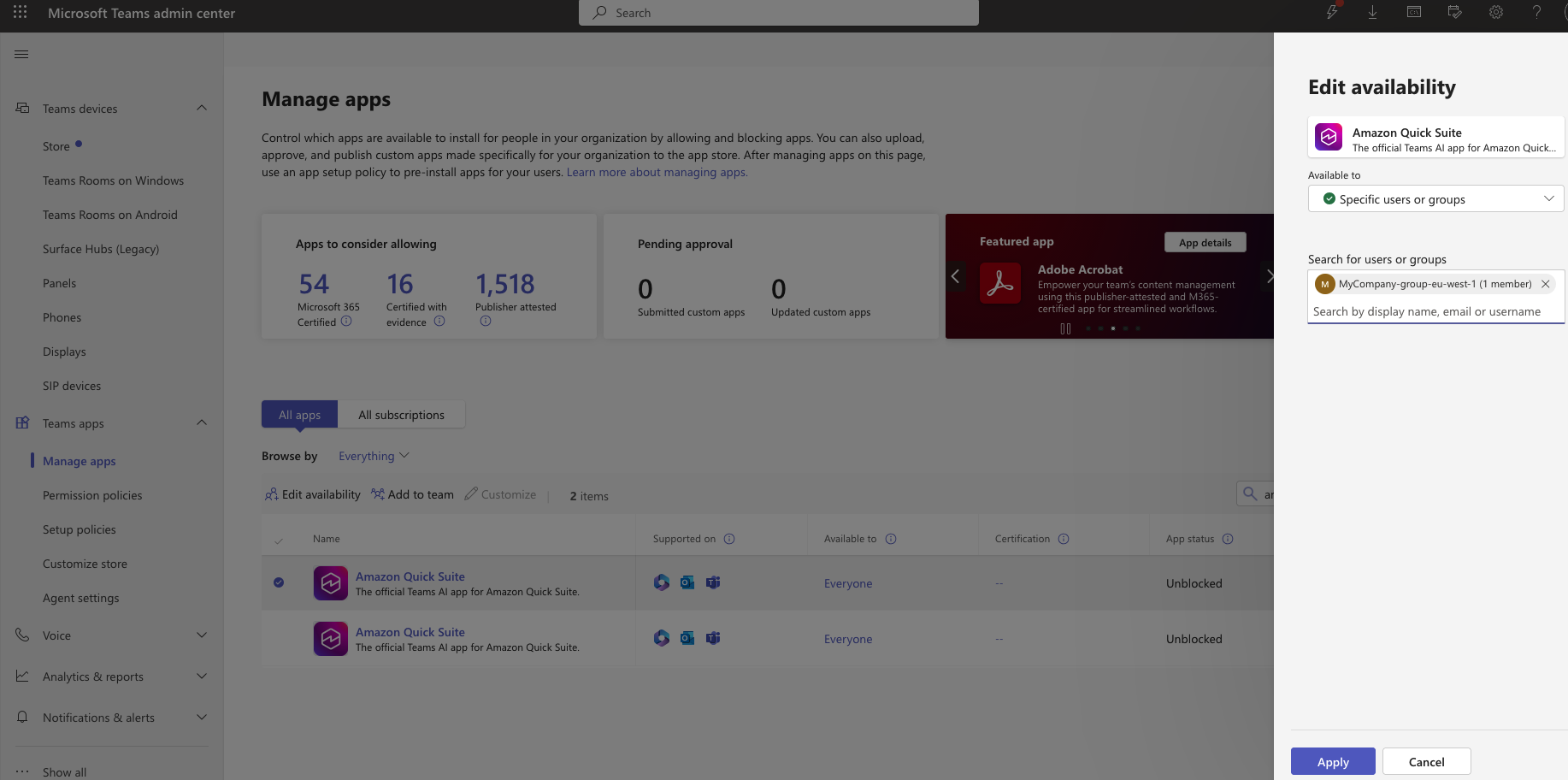
- Repeat the identical course of with the Microsoft Groups utility in
us-east-1Area.
The next screenshot exhibits what the configuration will appear to be in Microsoft Groups Admin Middle.
After deployment propagates, you’ll be able to validate that customers are robotically routed to the proper Regional agent.
Confirm the implementation
EU customers can use MyCompany-Groups-eu-west-1 agent when they’re interacting with the Microsoft Groups extension. The plugin will choose the My Assistant chat agent as default, so you could select the settings (gear) icon and select the MyCompany-Data-Agent-eu-west-1 chat agent.
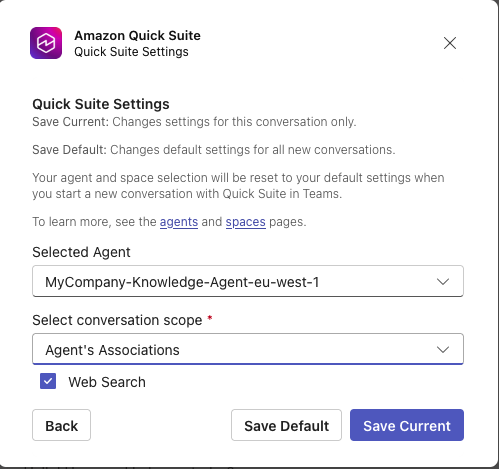
The next screenshot exhibits an instance of interacting with the chat agent.
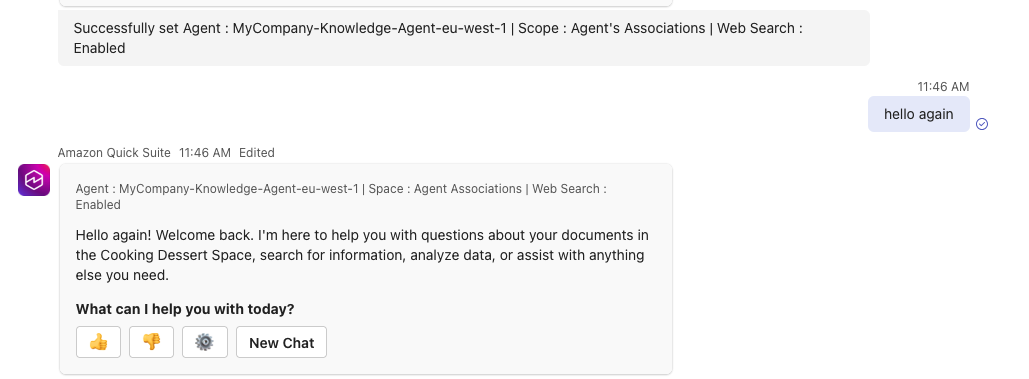
US customers can use the MyCompany-Data-Agent-us-east-1 chat agent, demonstrating profitable Regional routing with out guide configuration.
Troubleshooting
The next suggestions may also help you troubleshoot some widespread points you would possibly encounter whereas organising Amazon Fast extensions:
- Fast extension doesn’t present in Microsoft Groups:
- Wait 24–48 hours for Microsoft 365 deployment propagation
- Confirm the person is within the right Microsoft Entra ID group
- Clear the Microsoft Workplace add-on cache and restart Groups
- Points with authentication in Amazon Fast extension:
- Confirm the redirect URLs match precisely in Microsoft Entra ID
- Examine the trusted token issuer configuration
- Verify the IAM function belief relationship consists of the proper service principal
- Flawed agent listed within the Amazon Fast extension:
- Confirm person group membership (ought to solely be in a single Regional group)
- Examine the manifest-to-group task in Microsoft 365 Admin Middle
- Have the person signal out and check in once more
- The brokers drop-down checklist within the Amazon Fast extension is empty:
- Validate the agent is shared with customers on the Amazon Fast console
- Confirm the agent exists in the identical AWS Area because the extension
- Examine agent permissions are set to no less than Person degree
Clear up
To keep away from ongoing expenses, clear up the assets you created as a part of this submit when you now not want them.
Conclusion
This multi-Area Amazon Fast extension resolution for Microsoft 365 offers compliant, AWS Area-aware AI capabilities to your world workforce. The structure and implementation steps on this submit present combine enterprise AI with productiveness instruments whereas sustaining information residency and compliance boundaries.
For extra particulars on AI-powered assistants that improve productiveness with out switching functions, discuss with Extension entry. Discuss with Getting began with Amazon Fast to start out utilizing Amazon Fast at present.
Concerning the authors