AI brokers in manufacturing environments usually want to succeed in inside APIs, databases, and personal sources that sit behind Amazon Digital Personal Cloud (Amazon VPC) boundaries. Managing non-public connectivity for every agent-to-tool path provides operational overhead and slows deployment. Amazon Bedrock AgentCore VPC connectivity is designed to deploy AI brokers and Mannequin Context Protocol (MCP) servers with out requiring the community site visitors to be uncovered to the general public web. This functionality extends to managed Amazon VPC egress for Amazon Bedrock AgentCore Gateway, so you’ll be able to hook up with endpoints inside non-public networks throughout your AWS surroundings.
On this put up, you’ll configure Amazon Bedrock AgentCore Gateway to entry non-public endpoints utilizing Useful resource Gateway, a managed assemble that provisions Elastic Community Interfaces (ENIs) immediately inside your Amazon VPC, one per subnet. You’ll discover two implementation modes (managed and self-managed) and stroll by three sensible eventualities: connecting to a non-public Amazon API Gateway endpoint, integrating with a MCP server on Amazon Elastic Kubernetes Service (Amazon EKS), and accessing a non-public REST API.
Key phrases
The next phrases are used all through this put up. Evaluate them earlier than continuing to grasp how every part suits into the AgentCore Gateway VPC egress structure.
Useful resource VPC: The Amazon VPC the place your non-public useful resource lives. For instance, the VPC containing your privately hosted MCP server or API endpoint. That is the Amazon VPC that AgentCore Gateway wants to succeed in. Useful resource VPC can both be in the identical AWS account because the AgentCore Gateway account or in a special account.
AgentCore Gateway account: The AWS account the place you create and handle your AgentCore Gateway sources. This account might or might not be the identical account because the Useful resource VPC.
Useful resource Gateway: Useful resource gateway acts because the non-public entry level into your Useful resource VPC. When created, it provisions one ENI per subnet that you just specify, every sitting inside your VPC. Site visitors from AgentCore Gateway to your non-public useful resource arrives by these ENIs.
Useful resource Configuration: Useful resource configuration for VPC sources defines the particular useful resource AgentCore Gateway is allowed to succeed in by the Useful resource Gateway, recognized by a site identify, or IP handle. Moderately than granting entry to your complete Amazon VPC, a Useful resource Configuration scopes connectivity to a single endpoint.
Service Community Useful resource Affiliation: A service community useful resource affiliation connects a useful resource configuration to the AgentCore service community, which permits AgentCore Gateway service to invoke your non-public endpoint. AgentCore creates and manages this affiliation in your behalf, no matter which mode you utilize.
How does AgentCore Gateway VPC egress work?
AgentCore Gateway VPC egress helps two modes relying on how a lot management you need over the underlying networking infrastructure and the way you need to architect for cross-VPC connectivity.
Managed VPC useful resource
On this mode, AgentCore Gateway handles the whole lot in your behalf. You present your VPC ID, subnet IDs, and safety teams as a part of your goal configuration, and AgentCore robotically creates and manages the VPC Useful resource Gateway in your account. This mode integrates with present community architectures, whether or not you utilize VPC peering for same-Area or cross-Area connectivity or a hub-and-spoke mannequin with AWS Transit Gateway for multi-VPC and hybrid environments.
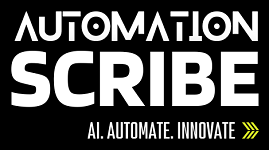
The next structure reveals how AgentCore Gateway connects to personal Amazon API Gateway utilizing managed VPC useful resource mode.
While you create an AgentCore Gateway Goal with a managed VPC useful resource configuration, AgentCore Gateway initiates the request and routes it to the Useful resource Gateway inside your Useful resource Proprietor VPC. The Useful resource Gateway forwards site visitors by an ENI provisioned in your subnet, ruled by the safety teams you configure. From the ENI, the request reaches the execute-api VPC endpoint. In managed VPC Useful resource mode, AgentCore creates and manages the Useful resource Gateway in your behalf, you solely have read-only visibility into it.
Self-managed Lattice useful resource
On this mode, you create and handle the VPC Lattice Useful resource Gateway and Useful resource configuration earlier than referencing it throughout goal creation on AgentCore Gateway. This provides you visibility and management over the Useful resource configuration, together with the variety of IPv4 addresses per ENI, subnet placement, and safety group guidelines. Extra importantly, it provides you visibility into the useful resource configuration itself, with the flexibility to view it, share it utilizing AWS Useful resource Entry Supervisor (AWS RAM) (required for cross-account connectivity), see associations tied to it, and retain the flexibility to revoke these associations while you select.
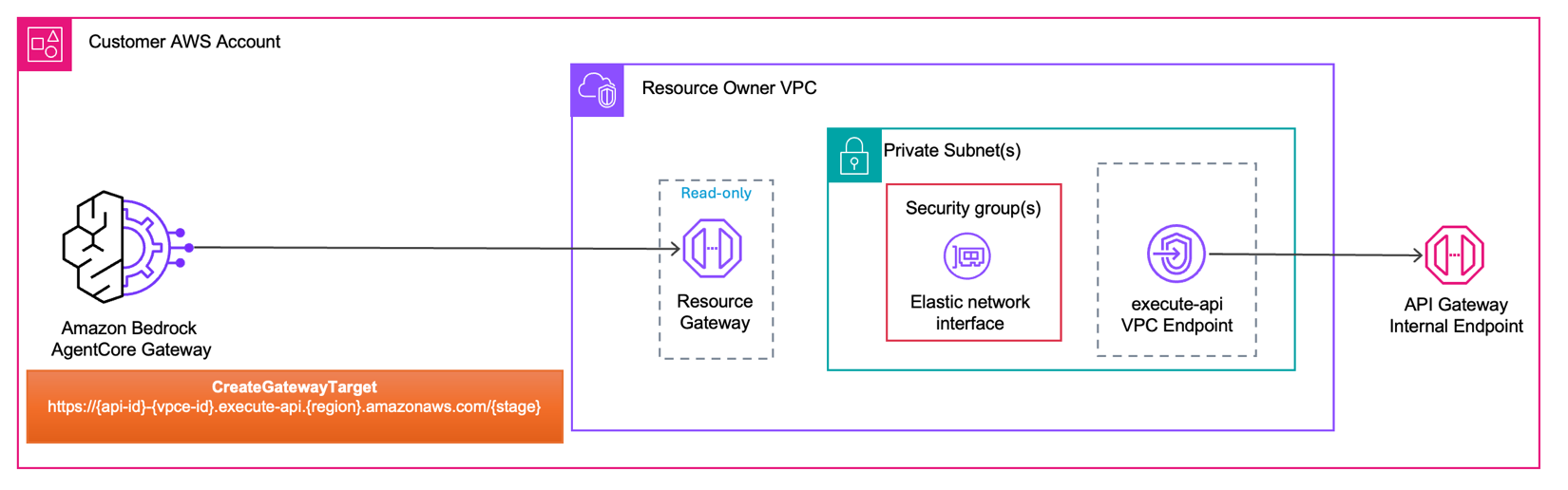
The next structure reveals how AgentCore Gateway connects to personal Relaxation API endpoints utilizing self-managed lattice useful resource mode.
In self-managed lattice useful resource mode, you pre-create the Useful resource Gateway and Useful resource Configuration earlier than configuring your AgentCore Gateway Goal. While you name CreateGatewayTarget, you go the Useful resource Configuration ID to affiliate AgentCore Gateway goal together with your non-public endpoint. At invocation time, Useful resource Gateway forwards the request by an ENI provisioned in your subnet, ruled by the safety teams you configure. From the ENI, the request reaches the execute-api VPC endpoint. Not like managed VPC Useful resource mode, you personal and handle the Useful resource Gateway and Useful resource Configuration.
Use the next desk to find out which mode suits your structure. Select managed VPC useful resource mode for streamlined setup, or self-managed Lattice useful resource mode for management over Useful resource Gateway lifecycle, cross-account connectivity, and visibility into associations.
| Dimension | AgentCore Managed VPC Useful resource | Self-Managed Lattice Useful resource |
| Setup complexity | Simple; present VPC ID, subnet IDs, and safety group IDs. AgentCore manages the remainder | Superior; you create and handle the Amazon VPC Lattice Useful resource Gateway and Useful resource Configurations your self, then go the useful resource configuration ID to every goal |
| IPv4 consumption | Every managed useful resource gateway consumes 1 IP handle per ENI. This isn’t configurable | When used with Amazon Bedrock AgentCore, it consumes one IP handle per subnet. If additionally hooked up to different VPC Lattice service networks, it consumes further IPs primarily based on the ipv4AddressesPerEni worth on the useful resource gateway |
| Cross-account | Not natively supported use hub-and-spoke architectures (VPC peering or AWS Transit Gateway ) for cross-account / cross-VPC eventualities. | Supported with AWS Useful resource Entry Handle (AWS RAM). Allows direct cross-account connectivity with out requiring VPC peering or Transit Gateways. |
| Reusing present ENIs | AgentCore robotically reuses one Useful resource Gateway (and its ENIs) throughout targets within the account whose managedVpcResource config matches on Amazon VPC, subnet set, security-group set, tags, and IP handle sort | You connect a number of Useful resource Configurations to a single Useful resource Gateway you personal; goal whose resourceConfigurationIdentifier resolves to that Useful resource Gateway shares its ENIs |
| Useful resource Gateway Lifecycle administration | Amazon Bedrock AgentCore creates, reuses, and deletes Useful resource Gateways in your behalf | You personal the total lifecycle of useful resource gateways and useful resource configurations |
| Governance and visibility | Useful resource Configurations are managed within the Amazon Bedrock AgentCore service account and aren’t seen in your Amazon VPC console. The underlying Useful resource Gateway is seen in your account in read-only mode | Full visibility into Useful resource Configurations, Service Community associations, and linked domains in your Amazon VPC Lattice console. You possibly can audit connections and revoke entry at a granular degree |
| Pricing | Per-GB knowledge processing costs solely (for knowledge processed by the Useful resource Gateway) | 1) Hourly cost for Service Community association2) Per-GB knowledge processing costs |
Get began with AgentCore Gateway VPC egress
On this put up, you deal with the managed VPC useful resource mode. If you wish to discover the self-managed lattice useful resource providing, observe the code samples. Earlier than getting began, this put up assumes fundamental familiarity with Amazon VPC, AWS Command Line Interface (AWS CLI), Amazon Bedrock AgentCore, and Amazon Bedrock AgentCore Gateway. Just be sure you have the next in place.
At present AgentCore Gateway’s trusts publicly signed TLS certificates; it doesn’t belief certificates signed by a non-public CA, so the handshake to your backend fails. In case your endpoint is protected by a non-public or self-signed certificates, discover the working answer pattern on GitHub.
Your IAM principal wants the iam:CreateServiceLinkedRole permission for bedrock-agentcore.amazonaws.com, in order that AgentCore can create the service-linked position in your behalf if it doesn’t exist already. For the required IAM coverage, see Gateway service-linked position.
The Useful resource Gateway safety group controls what site visitors the Useful resource Gateway ENIs can ship outbound to sources inside your Amazon VPC. Should you don’t present the safety group whereas invoking CreateGatewayTarget API, then the default safety group is used.
This walkthrough assumes that you’ve got an present AgentCore Gateway. Should you haven’t created one but, run:
Notice the gatewayId from the response. You want it when creating AgentCore Gateway Targets within the steps that observe.
- For in-depth examples, see the GitHub repository .
Personal Amazon API Gateway
On this part, you create an AgentCore Gateway goal that routes to a non-public Amazon API Gateway. Name the CreateGatewayTarget API with the next parameters. Within the openApiSchema discipline, present your non-public Amazon API Gateway endpoint URL (https://{api-id}-{vpce-id}.execute-api.{area}.amazonaws.com/{stage}). Within the managedVpcResource block, present your VPC ID, subnet IDs, and safety group ID.
After you run the command, AgentCore Gateway makes use of its service-linked position to provision a Useful resource Gateway in your VPC, creating one ENI per subnet you specified.
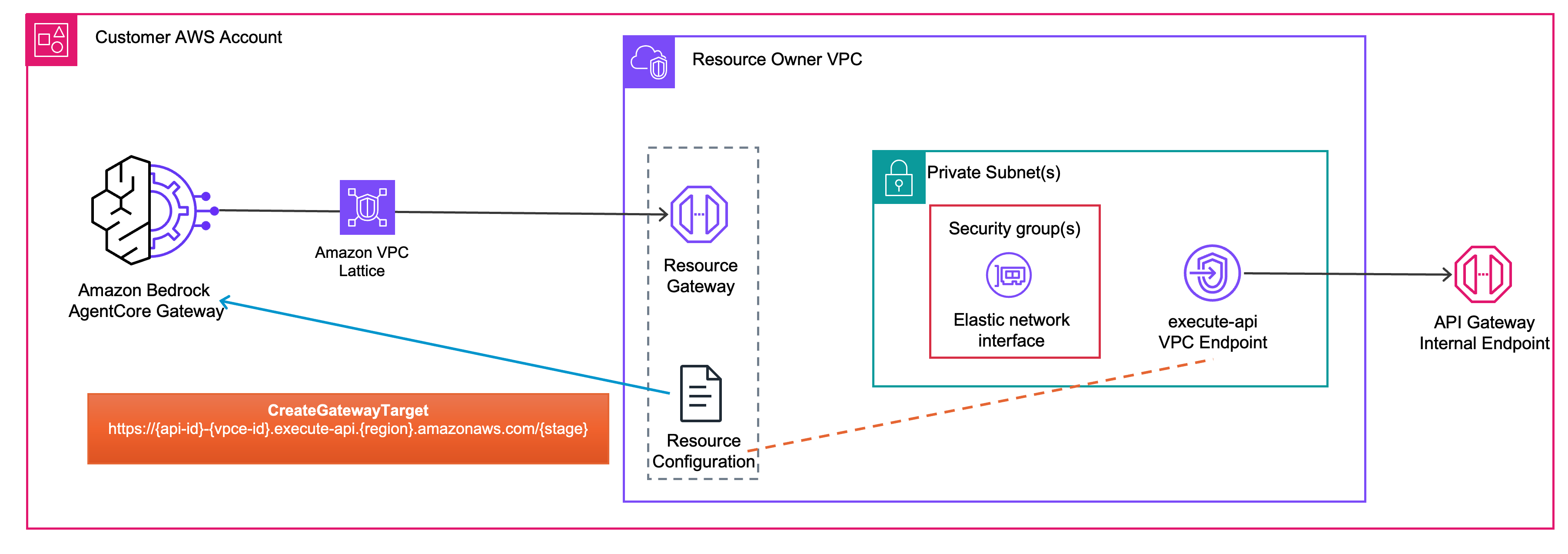
The next structure diagram reveals the community movement.
AgentCore Gateway initiates the request and routes it to the Useful resource Gateway provisioned inside Useful resource Proprietor VPC. Site visitors passes by the ENI inside your non-public subnet, the place your safety group guidelines govern what reaches the following hop. From there, the request reaches the execute-api VPC endpoint, which offers non-public connectivity to your Amazon API Gateway inside endpoint. The endpoint URL format https://{api-id}-{vpce-id}.execute-api.{area}.amazonaws.com/{stage} is what you supplied within the openApiSchema discipline of your CreateGatewayTarget name.
Personal MCP server on Amazon EKS
On this part, you create an AgentCore Gateway goal that routes to a non-public MCP server operating on Amazon EKS. Name the CreateGatewayTarget API with the next parameters. Within the mcpServer block, present your inside MCP server endpoint URL. Within the managedVpcResource block, present your VPC ID, subnet IDs, and safety group ID.
After you run this command, AgentCore provisions a Useful resource Gateway in your VPC, creating one ENI per subnet you specified. The next structure diagram reveals the end-to-end site visitors path.
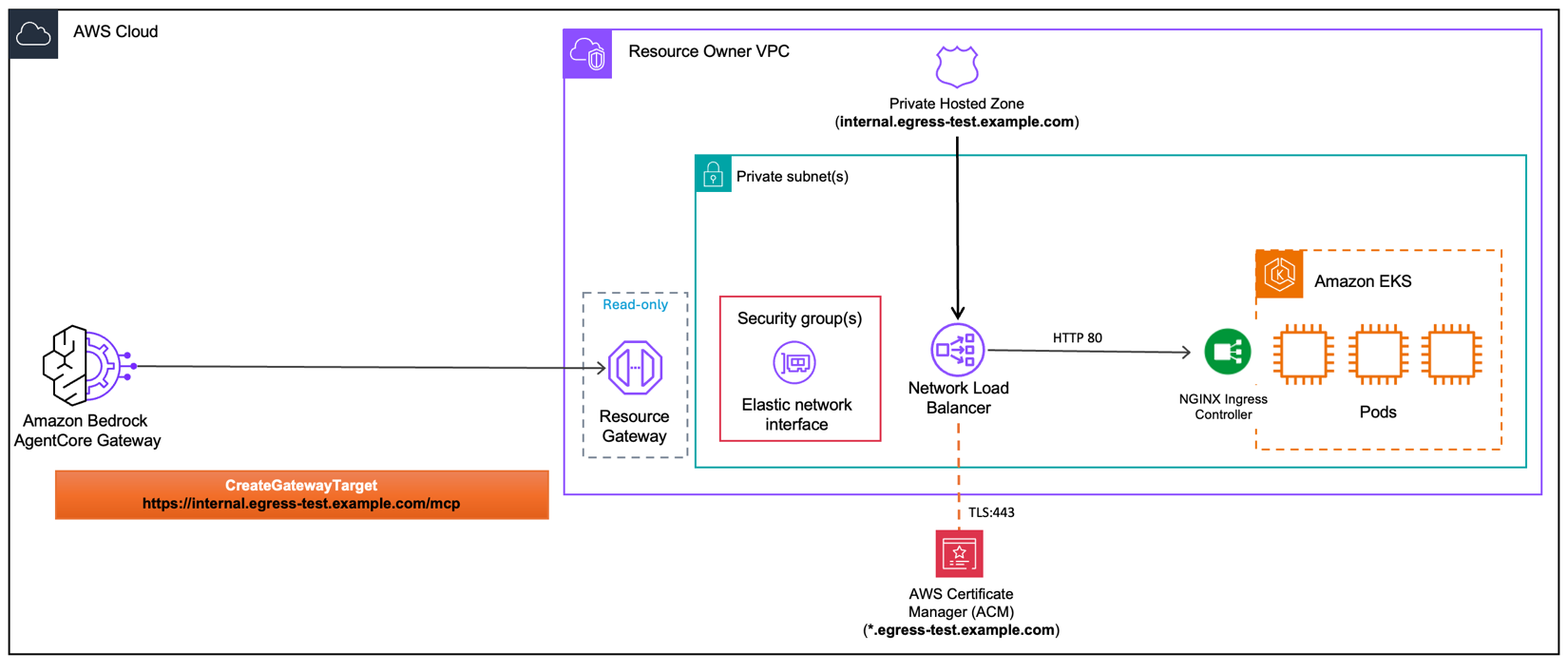
AgentCore Gateway sends an HTTPS request to your inside endpoint. The Amazon Route 53 non-public hosted zone resolves that area to the interior Community Load Balancer (NLB). The request enters the Useful resource Proprietor VPC by the Useful resource Gateway, passes by the ENI ruled by your safety teams, and arrives on the NLB. The NLB terminates TLS on port 443 utilizing an AWS Certificates Supervisor (ACM) public certificates, then forwards the request over HTTP on port 80 to the NGINX Ingress Controller operating on Amazon EKS, which routes it to the suitable pod.
Personal REST API goal
On this part, you create an AgentCore Gateway goal that routes to a non-public REST API endpoint. This is applicable to any REST API operating inside your Amazon VPC equivalent to a containerized microservice. The CreateGatewayTarget API name follows the identical sample because the earlier sections. Within the openApiSchema discipline, present your OpenAPI schema describing the REST API. Within the managedVpcResource block, present your VPC ID, subnet IDs, and safety group ID. After AgentCore Gateway provisions the Useful resource Gateway in your VPC, the next structure diagram reveals the end-to-end site visitors path.
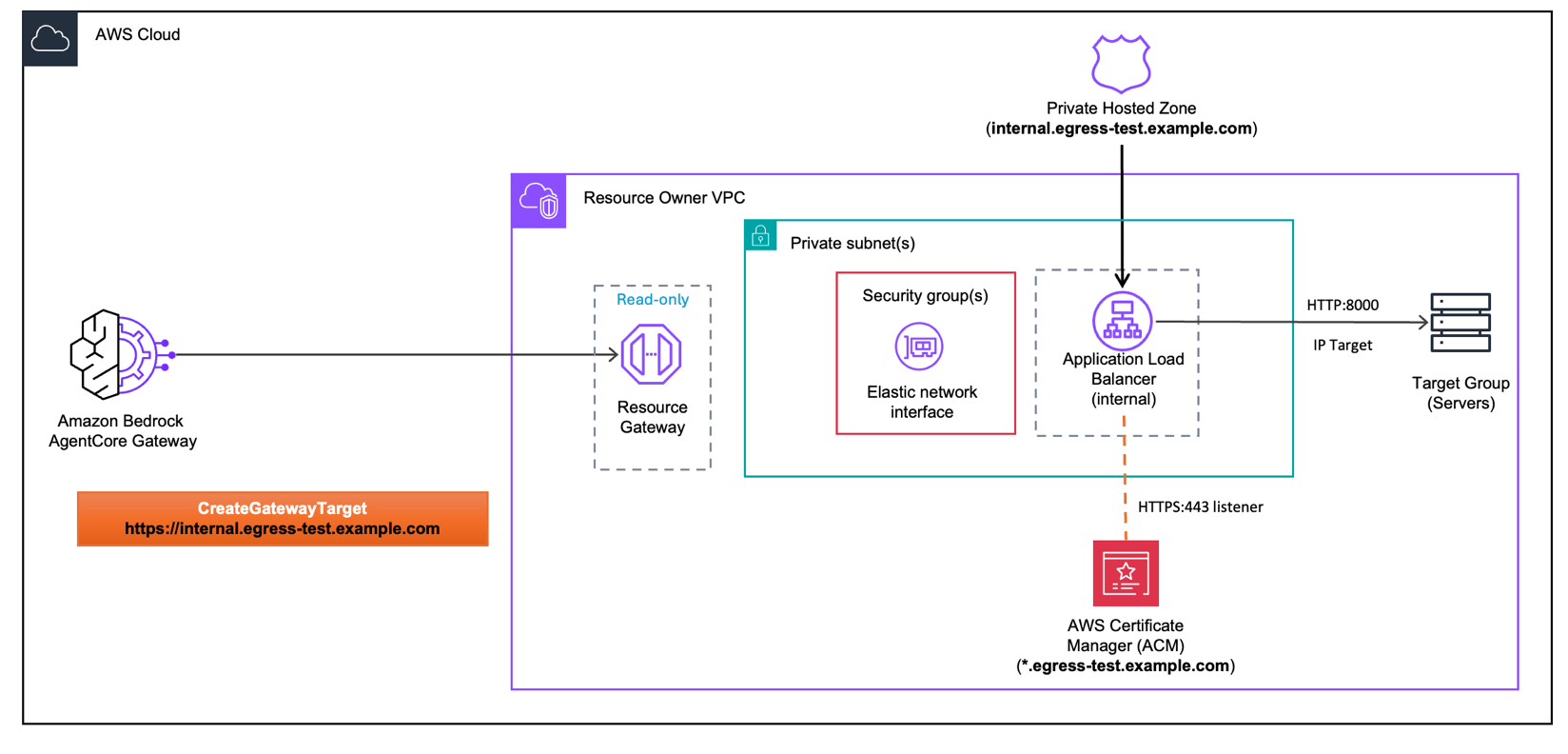
AgentCore Gateway sends an HTTPS request to your inside endpoint. The Amazon Route 53 non-public hosted zone resolves that area to the interior Utility Load Balancer (ALB). The request enters the Useful resource Proprietor VPC by the Useful resource Gateway, passes by the ENI ruled by your safety teams, and arrives on the inside ALB. The ALB terminates TLS on port 443 utilizing an AWS Certificates Supervisor (ACM) public certificates, then forwards the request over HTTP on port 8000 to the goal group containing your backend servers.
Clear up
To keep away from ongoing costs, delete all sources created on this walkthrough. For reference, see the AgentCore Gateway VPC egress pricing web page. Moreover, Amazon EKS clusters, load balancers, and API Gateway endpoints incur costs whereas operating. Confirm that your sources are deleted to cease costs. Should you adopted the GitHub pattern, be sure that to run the cleanup part on the finish of every Jupyter Pocket book.
Should you used managed VPC useful resource mode, deleting the Gateway Goal removes the related Amazon VPC Useful resource Gateway.
Conclusion
As AI brokers tackle extra complicated duties, they want safe entry to the instruments and companies that energy your enterprise, lots of which stay inside non-public networks. AgentCore Gateway VPC egress permits your brokers to succeed in non-public MCP servers, inside APIs, databases, and on-premises programs with out exposing them to the general public web.Managed VPC useful resource mode integrates immediately together with your present VPC and requires minimal configuration. Self-managed lattice useful resource mode provides you fine-grained management however requires further setup. Each route site visitors by a Useful resource Gateway that doesn’t go away the AWS community.
Subsequent steps
- Determine one inside API or MCP server in your surroundings that might profit from AI agent entry
- Evaluate your present Amazon VPC structure to find out which mode (Managed VPC Useful resource or Self-Managed Lattice Useful resource) suits your necessities
- Evaluate the Amazon Bedrock AgentCore Gateway documentation for added configuration choices
- Discover the Amazon VPC Lattice Useful resource Gateway documentation for cross-account eventualities
- Discover further integration patterns and superior configurations, see GitHub samples.
In regards to the authors
 Eashan Kaushik is a Specialist Options Architect AI/ML at Amazon Net Providers. He’s pushed by creating cutting-edge generative AI options whereas prioritizing a customer-centric strategy to his work. Earlier than this position, he obtained an MS in Pc Science from NYU Tandon College of Engineering. Outdoors of labor, he enjoys sports activities, lifting, and operating marathons.
Eashan Kaushik is a Specialist Options Architect AI/ML at Amazon Net Providers. He’s pushed by creating cutting-edge generative AI options whereas prioritizing a customer-centric strategy to his work. Earlier than this position, he obtained an MS in Pc Science from NYU Tandon College of Engineering. Outdoors of labor, he enjoys sports activities, lifting, and operating marathons.
 Thomas Mathew Veppumthara is a Sr. Software program Engineer at Amazon Net Providers (AWS) with Amazon Bedrock AgentCore. He has earlier generative AI management expertise in Amazon Bedrock Brokers and almost a decade of distributed programs experience throughout Amazon eCommerce Providers and Amazon Elastic Block Retailer (Amazon EBS). He holds a number of patents in distributed programs, storage, and generative AI applied sciences.
Thomas Mathew Veppumthara is a Sr. Software program Engineer at Amazon Net Providers (AWS) with Amazon Bedrock AgentCore. He has earlier generative AI management expertise in Amazon Bedrock Brokers and almost a decade of distributed programs experience throughout Amazon eCommerce Providers and Amazon Elastic Block Retailer (Amazon EBS). He holds a number of patents in distributed programs, storage, and generative AI applied sciences.
Rohin Meduri is a Software program Engineer at Amazon Net Providers (AWS) with Amazon Bedrock AgentCore. He has earlier AI improvement expertise with Amazon Bedrock Brokers and Amazon Lex. Earlier than this position, he obtained a BS in Pc Science from the College of Washington. Outdoors of labor, he enjoys chess, pool, and music manufacturing.
is a Software program Engineer at Amazon Net Providers (AWS) with Amazon Bedrock AgentCore. He has earlier AI improvement expertise with Amazon Bedrock Brokers and Amazon Lex. Earlier than this position, he obtained a BS in Pc Science from the College of Washington. Outdoors of labor, he enjoys chess, pool, and music manufacturing.